7 Critical Vulnerabilities We Found in SaaS Applications (Real Case Studies)
SaaS buyers do not lose deals because a product is “probably fine.” They lose deals when a security review turns up tenant data exposure, weak access control, or an API that leaks more than it should. The hard truth is that the most expensive SaaS security failures rarely start with a dramatic zero-day. They start with ordinary issues that were missed during development, missed by scanners, and only found when a real attacker or a serious customer review pushes deeper.
That is exactly why the keyword SaaS security vulnerabilities matters to founders, CTOs, and security leads. It is not an abstract search term. It is a board-level risk signal. OWASP’s Top 10 remains the best-known reference for the most critical web application risks, and AICPA’s SOC 2 guidance focuses on controls tied to security, availability, confidentiality, processing integrity, and privacy. In other words, the vulnerabilities that hurt SaaS companies are the same ones that slow audits, stall procurement, and create real breach exposure.

If you want a fast first pass before a full review, start with our free website vulnerability scanner. It will not replace a manual assessment, but it can help you spot obvious exposure early. For deeper validation, our web application penetration testing and API penetration testing services are built for SaaS environments where access control, business logic, and multi-tenant boundaries matter.
Problem: SaaS applications look secure until they are tested like an attacker would test them
Most SaaS teams have the basics in place. They use authentication, role-based access, logging, and a few automated scans before launch. The problem is that modern SaaS risk is rarely about one missing control. It is about combinations: a weak object reference here, an overly broad API token there, a search endpoint that trusts user input, or an admin function that can be reached from the wrong role.
In our engagements at Pentest Testing Corp, the most damaging findings are usually not flashy. They are quiet. A user can access another tenant’s invoice. A support role can reach an admin-only export. A request parameter can be modified to retrieve records that should never leave the account boundary. Those are the kinds of SaaS security vulnerabilities that turn into failed security reviews, breach notifications, and customer churn. Our own web testing and platform pages focus on exactly those issues: auth bypass, broken access control, business logic abuse, and API authorization flaws.
Risk: One overlooked flaw can become a revenue problem, not just a security problem
A SaaS breach is rarely a clean, isolated event. It becomes a commercial problem fast. Enterprise buyers ask for proof. Existing customers ask for reassurance. Auditors ask for evidence. Sales teams get dragged into security questionnaires. The longer the issue sits unresolved, the more damage it does.
We see this pattern often in SaaS security reviews: a single weakness turns into a chain. An attacker starts with an IDOR, pivots into another tenant’s data, then combines that with an API weakness to extract records at scale. What looked like a “small bug” becomes a reportable incident, a trust issue, and a compliance headache. AICPA’s SOC 2 framework is built around control assurance for security and related trust criteria, so weaknesses that affect data protection and access control directly undermine the story you need to tell auditors and customers.
Real-world attack scenario: how a low-friction SaaS breach happens
Imagine a customer success dashboard with an endpoint like /api/invoices?id=18422. The UI only shows a user their own invoice. The developer assumes the front end will protect the flow. A scanner sees nothing obvious. But a tester changes the ID and discovers another customer’s invoice. That is IDOR. If the same application also exposes a bulk export endpoint or a search filter that accepts unrestricted parameters, the issue can expand into broader data exposure.
Now add one more flaw. The application has an admin or support feature guarded only by a hidden front-end button. The back end never properly checks the role. Suddenly, the attacker can not only view another tenant’s records, but also change statuses, trigger exports, or pull sensitive audit data. This is how SaaS security vulnerabilities become a real incident. It is also why our services overview emphasizes real attack surface, not just surface-level scanning.
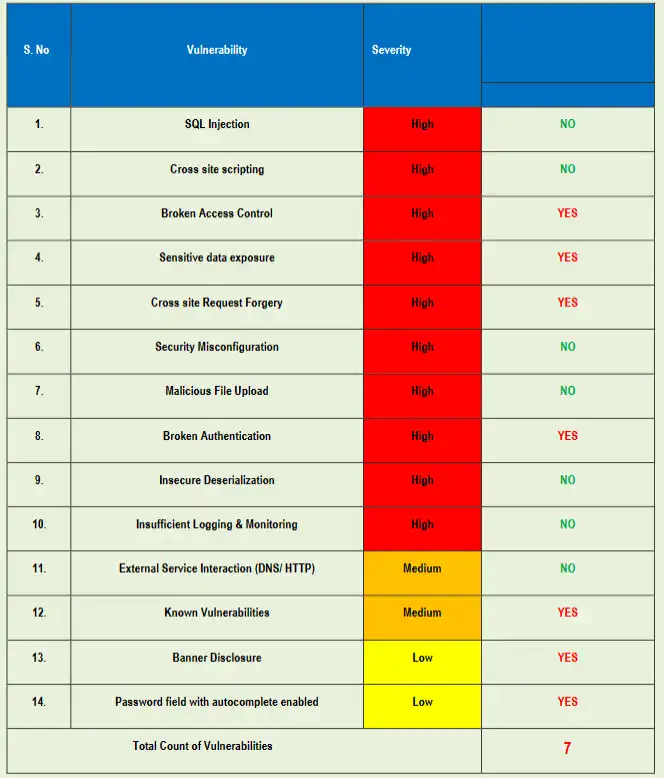
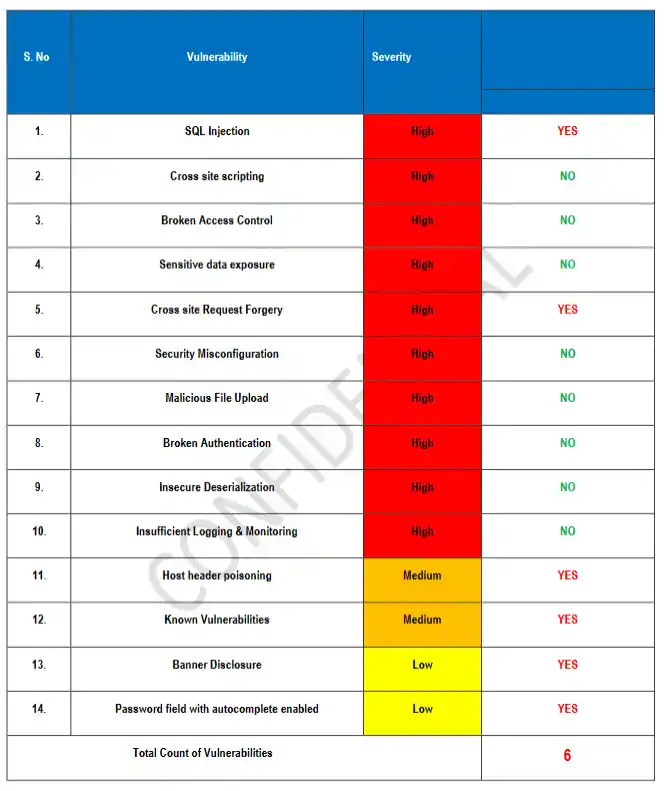
The seven vulnerabilities that keep showing up
- SQL injection in legacy or overlooked endpoints.
- IDOR in tenant-scoped records, invoices, tickets, and exports.
- Broken access control in admin, support, and internal workflows.
- API abuse through weak object-level authorization.
- Authentication flaws around reset links, sessions, or magic-link flows.
- Business logic abuse in billing, quotas, trial extensions, or approvals.
- Sensitive data exposure through logs, downloads, debug responses, or misconfigured cloud storage.
These are not theoretical. They are the exact categories that commonly surface in a manual web or API assessment, especially in SaaS platforms with multiple roles and integrations. OWASP’s Top 10 exists because these recurring patterns keep hurting real applications, and the 2025 release continues that focus on the most critical risks.
How attackers exploit these weaknesses
Attackers do not need a long exploit chain if the application gives them easy leverage. They test whether one user can reach another user’s object. They probe whether a role check happens in the UI only or actually on the server. They replay requests with different IDs, roles, tokens, and parameters. They look for places where the product assumes a trusted client.
That is why an attacker can often bypass “secure-looking” SaaS systems without brute force or malware. They simply use the application the way the application was not meant to be used. The strongest clue is usually repetition: if one account can act on another account’s data, the bug is already business-critical. Our API penetration testing service is built to validate those object-level and workflow-level gaps before customers or attackers do.
Why automated tools miss critical vulnerabilities
Automated scanners are useful, but they are not enough for SaaS. They are strong at finding known signatures, obvious injection points, missing headers, and straightforward misconfigurations. They are much weaker at following state changes, chained requests, role confusion, and logic abuse. That is where the real losses usually happen.
Through our service pages, we explicitly emphasize manual-first testing, reduced false positives, and real-world attack scenarios because those are the conditions that expose business logic flaws and access control failures. A scanner might tell you a page exists. A human tester tells you whether the page should exist for that user at all.
A good next step is to pair a light scan with a manual review of your highest-risk flows: login, invite acceptance, tenant switching, billing, exports, password reset, and API access. That is usually where the most expensive issues hide. For teams working toward enterprise procurement or SOC 2 readiness, manual validation is the difference between “we ran a scan” and “we proved the controls work.”
How penetration testing solves the problem
A proper penetration test goes beyond “findings.” It simulates how a real attacker would move through your SaaS product, then proves whether the issue is exploitable and how far it reaches. That means testing access controls, authorization boundaries, session handling, data exposure paths, API behavior, and business logic, not just isolated pages.
This matters because security teams need evidence they can act on. Product teams need repro steps they can fix. Leadership needs a business translation of the risk. That is the value of a focused assessment from a team that understands both the technical layer and the buyer layer. Our web application penetration testing and cloud penetration testing engagements are designed for exactly that kind of output.
What to look for in a penetration testing company, especially for SOC 2
If SOC 2 matters to your company, look for more than a logo and a checklist. You want a partner that understands how control testing maps to real SaaS risk. AICPA’s SOC 2 material is centered on trust services criteria, so your testing partner should be comfortable explaining findings in terms of security, availability, confidentiality, processing integrity, and privacy.
The best vendors will also give you developer-ready remediation, not vague advice. They will show you impact, proof, retest options, and what changed after the fix. We provide audit-ready evidence for SOC 2 and enterprise security reviews, which is exactly what buyers need when a deal or renewal is on the line.
Closing Note
If you are preparing for SOC 2, trying to close enterprise deals, or simply want confidence that your SaaS product is not exposing tenant data, the next step is a manual assessment that reflects how attackers actually work. Start with a quick scan if you need a baseline, then move into a deeper review of your web app and APIs before a customer, auditor, or attacker finds the gap first.
Schedule a conversation with Pentest Testing Corp for a focused SaaS security assessment. Our web penetration testing, API penetration testing, and cloud penetration testing services are built to find exploitable issues, explain business impact clearly, and give your team remediation steps they can act on fast.
🔐 Frequently Asked Questions (FAQs)
Find answers to commonly asked questions about SaaS Security Vulnerabilities.