Manual Penetration Testing Services for SOC 2, PCI DSS & HIPAA Compliance
We find the exploitable vulnerabilities that automated scanners miss. Every engagement is manual-first, conducted by certified professionals aligned to OWASP Top 10, PTES, and NIST SP 800-115, validated exploits, developer-ready remediation guidance, and compliance-mapped reporting, not a list of scanner alerts.
NDA available on request · Fixed-price quotes · No automated scan padding
153+ Engagements Delivered | 6,000+ Vulnerabilities Identified & Validated | 250+ Clients in 30+ Countries | SOC 2 · PCI DSS · HIPAA · ISO 27001 · GDPR
Trusted by Security-Conscious Teams Across SaaS, Fintech, Healthcare & E-Commerce








Clients span managed IT, dental & medical practice software, wealth management, food retail, and cloud platforms across North America, Europe, and beyond.
Find and Fix Exploitable Risks Before Auditors or Attackers Do
Your auditor needs evidence of a penetration test. Your enterprise customers want proof you take security seriously. Your development team needs actionable findings, not a 200-page PDF they’ll never read.
Most vendors hand you a scanner report dressed up in a PDF. We don’t. Every finding is manually exploited or attempted before it enters the report — real vulnerabilities, reproducible, tied to business risk. Reports are structured for your CISO, your developers, and your auditors simultaneously: shorter remediation cycles, cleaner audit evidence, security that holds up when it counts.
Bundled assessments: web + API, cloud + network, or full-stack, include a single scoping call, unified report, and coordinated timeline → Get a Bundled Quote
How We Test: A Methodology You Can Show Auditors
Phase 1: Scoping & Rules of Engagement
We define the attack surface, agree on testing windows and authentication scenarios, and issue written scope confirmation before any testing begins.
Phase 2: Reconnaissance & Threat Modeling
We map your architecture, enumerate entry points and your tech stack, and build a threat model tailored to your environment — not a generic checklist.
Phase 3: Exploitation & Validation (Manual-First)
Every potential finding is manually exploited or attempted before entering the report. Automated tools support discovery; human judgment decides what’s real.
Phase 4: Reporting & Remediation Guidance
Each finding includes a CVSS severity rating, reproduction steps, business impact statement, code- or configuration-level fix recommendation, and compliance mapping (SOC 2 CC6, PCI DSS Req. 11.3, and others) on request.
Phase 5: Retest & Closure
Optional retest confirms remediations are correctly implemented, providing documented closure evidence for auditors and enterprise customers.
Frameworks: OWASP Top 10 · OWASP API Security Top 10 · PTES · NIST SP 800-115 · MITRE ATT&CK
Penetration Testing Built for Compliance-Driven Teams
SOC 2 Type II: Findings map to Trust Services Criteria CC6.1, CC6.6, CC7.1, and CC8.1, with evidence packages structured for direct auditor submission.
PCI DSS v4.0: Requirement 11.3 mandates internal and external penetration testing of the cardholder data environment. We test full scope and document findings in PCI-compatible format.
HIPAA Security Rule: We assess technical safeguards and deliver findings that support your Security Risk Analysis (SRA) documentation.
ISO/IEC 27001:2022: Testing supports Annex A controls A.8.8 and A.8.29, formatted as risk treatment evidence.
GDPR: We identify vulnerabilities constituting technical failures under Article 32 and provide findings suitable for DPIA documentation.
Transparent, Fixed-Price Engagement Tiers
Fixed prices agreed before testing begins, no time-and-materials estimates, no scope creep surprises.
| Services | Starting From | Typical Timeline |
|---|---|---|
| Web Application Pentest | $5,000 | 5–8 business days |
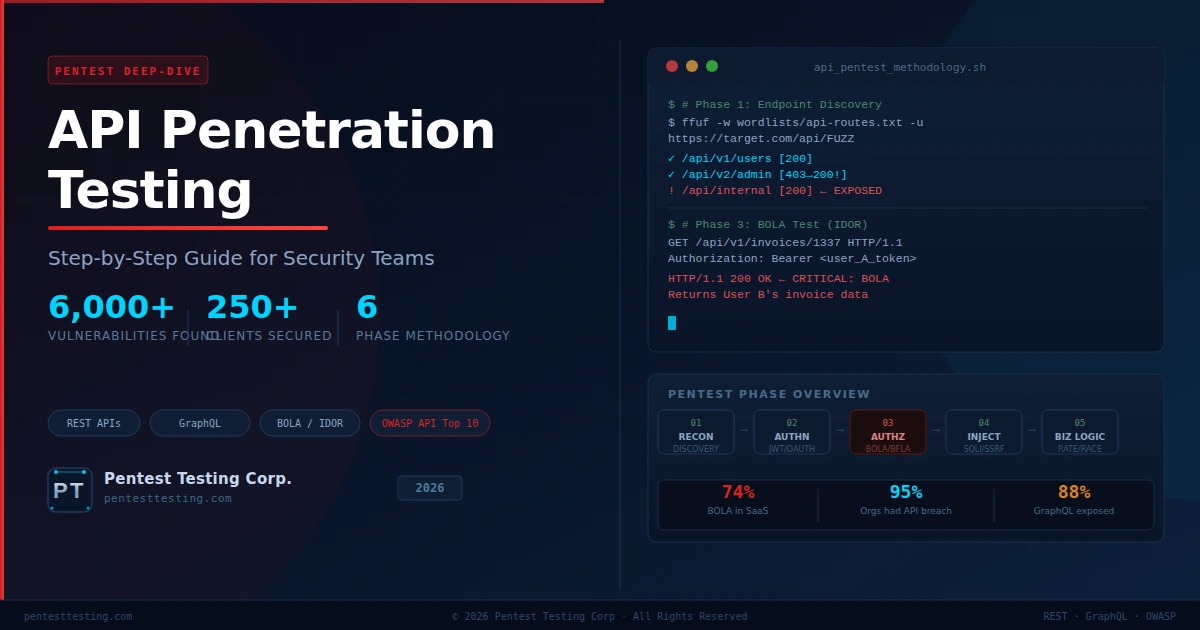
| API Penetration Testing | $5,000 | 4–7 business days |
| Mobile App Pentest (single platform) | $8,000 | 7–10 business days |
| Cloud Penetration Testing | $6,500 | 5–8 business days |
| External Network Pentest | $4,500 | 3–5 business days |
| Internal Network Pentest | From $6,000 | 5–8 business days |
Complex environments, microservices, or bundled engagements are quoted after a scoping call.
Continuous Penetration Testing (PTaaS) – Test as You Ship
Annual tests leave 11 months of untested exposure. Our PTaaS model aligns testing to your sprint and release cycle: on-demand testing as you ship new features, sprint-aligned findings with prioritized remediation, and cumulative compliance evidence building throughout the year. Designed for startups closing enterprise deals, scale-ups preparing for major releases, and enterprises that need continuous board-level risk reporting.
⭐ What Our Clients Say
Service: HIPAA Testing
Pentest Testing Corp conducted a comprehensive HIPAA-focused security assessment for Dentallive Planner with outstanding professionalism and technical expertise. Md Shofiur demonstrated a deep understanding of healthcare security requirements, identifying vulnerabilities that could have impacted sensitive patient data and compliance standards.
The testing process was detailed, well-structured, and the final report provided clear remediation guidance that was easy for our development team to implement. Communication throughout the engagement was excellent, and the overall experience exceeded our expectations.
Service: Web Application Penetration Testing
It was a pleasure working with Pentest Testing Corp. They delivered a high-quality penetration test for our web application with excellent attention to detail, professional communication, and fast turnaround time.
What impressed me most was their honesty and professionalism throughout the engagement. The final security report was detailed, official, and highly valuable for our internal security improvements.
Service: Call Center API Penetration Testing
Pentest Testing Corp conducted a comprehensive API penetration test for our call center platform with a high level of professionalism and technical expertise. The assessment was detailed, efficient, and uncovered important security issues that helped us strengthen the protection of our APIs and backend systems.
Why Compliance Teams Trust Our Process
Our testers hold certifications including OSCP, CEH, API Security for PCI Compliance, ISO/IEC 27001 Security Associate, and CompTIA Security+/CySA+. Every engagement begins with a signed NDA, yours or ours with rules of engagement documented before go-live. Test evidence is encrypted in transit and at rest, and all test data is destroyed or returned upon engagement completion.
Our Latest Research & Articles
Practical security research and playbooks focused on real attack paths in web apps and APIs.
Frequently Asked Questions (FAQs)
Ready to Validate Your Security Before Your Next Audit?
Share your scope, and we'll respond within one business day with a fixed-price quote.