9 Powerful Forensic-Driven Security Hardening Steps (After Jan–Feb 2026 Bulletins)
Most teams patch fast during high-impact January/February 2026 security cycles—then move on. Attackers love that gap.
Because the real question isn’t “Did we patch?”
It’s “Can we prove we’re clean—and stay resilient—after patching?”
That’s what forensic-driven security hardening delivers: hardening choices that create verifiable evidence (not opinions) that endpoints, servers, and mobile fleets are both patched and not quietly owned.

Just released: CVE-2026-21509 Microsoft Office Zero-Day — a practical DFIR checklist covering immediate actions (first 24 hours), Office exploit detection signals on endpoints, rapid evidence capture (memory-first), and M365 mail/identity telemetry for scoping and containment.
https://www.pentesttesting.com/cve-2026-21509-office-zero-day-triage-dfir/
Why Jan–Feb 2026 bulletins changed “patch and forget”
Early 2026 bulletins reinforced a pattern we keep seeing in incident response:
- Mobile: Web rendering and embedded browser surfaces make “Safari-only” thinking obsolete. If iOS/iPadOS WebKit-class bugs are patched, risk spills into app webviews and link handlers across the device fleet.
- Android: patching is only real when devices report the expected security patch level and your MDM enforces compliance.
- Windows: Patch Tuesday cycles continue to include actively exploited classes of vulnerabilities (example: Desktop Window Manager (DWM) zero-day patterns), often chained with phishing, infostealers, or local privilege escalation.
So instead of treating patches as the finish line, treat them as the trigger for post-patch proof.
Step 1) Convert “patched” into a measurable policy (not a feeling)
Start with a baseline file that your team can reuse every month.
# post_patch_baseline.yaml
baseline_name: "Jan-Feb 2026 Hot Bulletin Baseline"
required_within_hours: 72
windows:
require:
- os_build_verified
- kb_installed_verified
- reboot_state_verified
- defender_or_edr_healthy
- persistence_hunt_completed
android:
min_security_patch_level: "2026-01-05"
require:
- mdm_export_saved
- compliance_scored
ios_ipados:
min_os_version: "26.2"
require:
- mdm_export_saved
- unknown_device_check_completedThis is the foundation of forensic-driven security hardening: every claim must be provable by a file you can retain.
Step 2) Build a “Patch Proof Pack” folder structure (standardize evidence)
Stop improvising evidence during audits and incidents. Standardize it:
Patch-Proof-Pack/
2026-02-Cycle/
00_Scope/
01_Change_Records/
02_Deployment_Logs/
03_Verification_Outputs/
04_Exceptions/
05_Compliance_Report/
06_Indicators_Triage/
07_Retention_Notes/
08_Hash_Manifest/Exceptions register (so “non-compliance” is controlled, not chaos)
# 04_Exceptions/exceptions.yaml
- asset: "LEGACY-APP-SERVER-01"
reason: "Vendor incompatibility with Feb 2026 update"
compensating_controls:
- "Inbound restricted to jump host"
- "No interactive logons; rotate service creds"
- "EDR set to strict + isolate-on-suspicion"
owner: "IT Manager"
review_date: "2026-02-20"This is how forensic-driven security hardening stays business-friendly: exceptions are explicit and time-bounded.
Step 3) Windows: export patch + build evidence (auditor-friendly)
Use PowerShell to collect proof that survives scrutiny.
# windows_patch_proof.ps1
$OutDir = "Patch-Proof-Pack\2026-02-Cycle\03_Verification_Outputs\Windows\$env:COMPUTERNAME"
New-Item -ItemType Directory -Force -Path $OutDir | Out-Null
# OS build evidence
(Get-ComputerInfo | Select-Object WindowsProductName, WindowsVersion, OsBuildNumber) |
ConvertTo-Json | Out-File "$OutDir\os_build.json" -Encoding utf8
# Hotfix evidence
Get-HotFix | Sort-Object InstalledOn -Descending |
Select-Object -First 50 |
Export-Csv "$OutDir\hotfix_last50.csv" -NoTypeInformation
# Update client operational log (best-effort)
try {
Get-WinEvent -LogName "Microsoft-Windows-WindowsUpdateClient/Operational" -MaxEvents 2000 |
Select-Object TimeCreated, Id, LevelDisplayName, Message |
Export-Csv "$OutDir\windows_update_events.csv" -NoTypeInformation
} catch {
"WindowsUpdateClient/Operational not available." | Out-File "$OutDir\windows_update_events_note.txt"
}
# Reboot evidence
(Get-CimInstance Win32_OperatingSystem | Select-Object LastBootUpTime) |
ConvertTo-Json | Out-File "$OutDir\last_boot.json" -Encoding utf8
Write-Host "OK: exported Windows patch proof to $OutDir"Fast integrity checks (post-patch sanity)
# Integrity quick checks (run as Admin)
sfc /scannow | Out-File ".\sfc_scannow.txt"
DISM /Online /Cleanup-Image /ScanHealth | Out-File ".\dism_scanhealth.txt"Step 4) Windows forensic hardening: turn on the logs you’ll wish you had
Forensic-driven security hardening means enabling high-signal telemetry before the incident.
A) Enable PowerShell logging (high value in real intrusions)
# Enable Script Block + Module logging (baseline-friendly)
New-Item -Path "HKLM:\SOFTWARE\Policies\Microsoft\Windows\PowerShell\ScriptBlockLogging" -Force | Out-Null
Set-ItemProperty -Path "HKLM:\SOFTWARE\Policies\Microsoft\Windows\PowerShell\ScriptBlockLogging" `
-Name "EnableScriptBlockLogging" -Value 1 -Type DWord
New-Item -Path "HKLM:\SOFTWARE\Policies\Microsoft\Windows\PowerShell\ModuleLogging" -Force | Out-Null
Set-ItemProperty -Path "HKLM:\SOFTWARE\Policies\Microsoft\Windows\PowerShell\ModuleLogging" `
-Name "EnableModuleLogging" -Value 1 -Type DWordB) Enable Security audit policy for logon + privilege signals
auditpol /set /subcategory:"Logon" /success:enable /failure:enable
auditpol /set /subcategory:"Special Logon" /success:enable /failure:enable
auditpol /set /subcategory:"Process Creation" /success:enable /failure:enable
auditpol /set /subcategory:"Account Lockout" /success:enable /failure:enableTip: Pair “Process Creation” with command-line logging via Group Policy to make it investigation-grade.
If you want DFIR experts to validate suspicious activity after patching, see our DFIR service page:
https://www.pentesttesting.com/digital-forensic-analysis-services/
Step 5) Linux: patch evidence + auditd rules you can retain
A) Patch evidence (Debian/Ubuntu)
# linux_patch_evidence_apt.sh
set -euo pipefail
OUTDIR="Patch-Proof-Pack/2026-02-Cycle/03_Verification_Outputs/Linux/$(hostname)"
mkdir -p "$OUTDIR"
uname -a > "$OUTDIR/uname.txt"
cat /etc/os-release > "$OUTDIR/os-release.txt"
dpkg-query -W -f='${Package},${Version}\n' | sort > "$OUTDIR/packages_installed.csv"
sudo cp /var/log/apt/history.log "$OUTDIR/apt_history.log" 2>/dev/null || true
sudo cp /var/log/dpkg.log "$OUTDIR/dpkg.log" 2>/dev/null || true
echo "OK: Linux patch evidence exported to $OUTDIR"B) Minimal auditd rules (high-signal)
# /etc/audit/rules.d/99-forensic-hardening.rules
-w /etc/passwd -p wa -k identity
-w /etc/shadow -p wa -k identity
-w /etc/sudoers -p wa -k scope
-w /etc/ssh/sshd_config -p wa -k sshd
# Track execve (be mindful of volume; tune for servers)
-a always,exit -F arch=b64 -S execve -k proc_execReload:
sudo augenrules --load
sudo systemctl restart auditdStep 6) Android: verify patch level + capture controlled evidence
A) Patch level verification (ADB)
# android_patch_verify.sh
set -euo pipefail
CASE_ID="${1:-CASE-ANDROID-001}"
OUT="Patch-Proof-Pack/2026-02-Cycle/03_Verification_Outputs/Android/$CASE_ID"
mkdir -p "$OUT"
adb devices
adb shell getprop ro.build.version.security_patch > "$OUT/security_patch_level.txt"
adb shell getprop ro.build.version.release > "$OUT/android_version.txt"
adb shell getprop ro.product.model > "$OUT/model.txt"
echo "OK: captured Android patch identifiers in $OUT"B) Evidence capture (best-effort, authorized use only)
# android_evidence_capture.sh
set -euo pipefail
CASE_ID="${1:-CASE-ANDROID-IR-001}"
OUT="Patch-Proof-Pack/2026-02-Cycle/06_Indicators_Triage/Android/$CASE_ID"
mkdir -p "$OUT"
adb shell pm list packages -f > "$OUT/packages.txt"
adb logcat -b all -d > "$OUT/logcat_all.txt" || true
adb bugreport > "$OUT/bugreport.zip" || true
echo "OK: captured Android triage artifacts in $OUT"Step 7) iOS/iPadOS: focus on what’s realistically collectible (and still useful)
iOS collection is constrained by design, but you can still do forensic-driven security hardening by standardizing what you can prove:
- MDM export (OS version, last check-in, compliance state, profiles)
- Unknown Apple ID / new device sign-in review
- Suspicious configuration profile checks (unexpected profiles)
- sysdiagnose (when your process supports it)
If you have a trusted pairing workflow:
# best-effort device metadata (requires trusted pairing)
CASE_ID="${1:-CASE-IOS-001}"
OUT="Patch-Proof-Pack/2026-02-Cycle/03_Verification_Outputs/iOS/$CASE_ID"
mkdir -p "$OUT"
ideviceinfo > "$OUT/ideviceinfo.txt" || true
echo "OK: wrote iOS device summary to $OUT"For a practical iPhone DFIR checklist, see:
https://www.pentesttesting.com/iphone-suspicious-activity-dfir-checklist/
Step 8) Score compliance automatically (so proof scales)
Turn MDM exports into an auditable compliance report.
# mobile_compliance_score.py
import csv
from datetime import datetime
BASELINE_ANDROID_SPL = "2026-01-05"
BASELINE_IOS = (26, 2)
def parse_ios(ver: str):
parts = (ver or "").split(".")
nums = []
for p in parts:
try:
nums.append(int(p))
except:
nums.append(0)
while len(nums) < 2:
nums.append(0)
return tuple(nums[:2])
def ios_ok(ver: str) -> bool:
return parse_ios(ver) >= BASELINE_IOS
def android_ok(spl: str) -> bool:
return (spl or "") >= BASELINE_ANDROID_SPL
checked_at = datetime.utcnow().isoformat() + "Z"
in_file = "mdm_mobile_inventory.csv"
out_file = "Patch-Proof-Pack/2026-02-Cycle/05_Compliance_Report/mobile_compliance.csv"
with open(in_file, newline="", encoding="utf-8") as f:
r = csv.DictReader(f)
rows = []
for row in r:
platform = (row.get("platform") or row.get("OperatingSystem") or "").lower()
os_version = row.get("os_version") or row.get("OsVersion") or ""
spl = row.get("security_patch_level") or row.get("AndroidSecurityPatchLevel") or ""
compliant = False
baseline = ""
if "android" in platform:
compliant = android_ok(spl)
baseline = f"Android SPL >= {BASELINE_ANDROID_SPL}"
elif "ios" in platform or "ipad" in platform:
compliant = ios_ok(os_version)
baseline = "iOS/iPadOS >= 26.2"
row["baseline"] = baseline
row["post_patch_compliant"] = "YES" if compliant else "NO"
row["checked_at"] = checked_at
rows.append(row)
fields = rows[0].keys() if rows else ["platform","os_version","security_patch_level","post_patch_compliant","checked_at"]
with open(out_file, "w", newline="", encoding="utf-8") as o:
w = csv.DictWriter(o, fieldnames=fields)
w.writeheader()
w.writerows(rows)
print(f"OK: wrote {out_file}")This is the difference between “we think we’re good” and forensic-driven security hardening you can defend to customers.
Step 9) Hash everything (prove integrity of your proof)
If evidence can be modified, it’s not evidence.
Windows hash manifest
# write_hash_manifest.ps1
$Root = "Patch-Proof-Pack\2026-02-Cycle"
$OutDir = Join-Path $Root "08_Hash_Manifest"
New-Item -ItemType Directory -Force -Path $OutDir | Out-Null
$Manifest = Join-Path $OutDir "sha256_manifest.txt"
Get-ChildItem -Path $Root -File -Recurse |
Where-Object { $_.FullName -notmatch '\\08_Hash_Manifest\\' } |
ForEach-Object {
$h = Get-FileHash -Algorithm SHA256 -Path $_.FullName
"{0} {1}" -f $h.Hash, ($h.Path.Replace($Root + "\", ""))
} | Out-File $Manifest -Encoding ascii
Write-Host "OK: wrote $Manifest"
SIEM/SOAR integration patterns (keep it simple)
Microsoft Sentinel (KQL) concept ideas
// Devices with recent suspicious process bursts after patch window (concept)
DeviceProcessEvents
| where Timestamp > ago(7d)
| summarize proc_count=count() by DeviceName
| where proc_count > 2000
| order by proc_count descSplunk concept idea
index=wineventlog Provider_Name="Microsoft-Windows-WindowsUpdateClient"
| stats count by host, EventCodeSOAR playbook skeleton
name: post_patch_proof_automation
triggers:
- endpoint_non_compliant
- suspicious_indicators_detected
actions:
- create_ticket:
title: "Post-patch validation failed: {{asset}}"
severity: high
attach:
- "Patch-Proof-Pack link"
- "sha256_manifest.txt"
- if: suspicious_indicators_detected
then:
- isolate_endpoint
- notify_soc
- start_dfir_intakeWhere risk assessment + remediation fit (so this becomes a lifecycle)
Forensic-driven security hardening works best when it’s part of a closed loop:
- Baseline risk → what matters most and why
https://www.pentesttesting.com/risk-assessment-services/ - Fix what’s real → eliminate the exploitable paths
https://www.pentesttesting.com/remediation-services/ - Prove clean → if signals look suspicious, escalate to DFIR
https://www.pentesttesting.com/digital-forensic-analysis-services/
Free Website Vulnerability Scanner tool dashboard
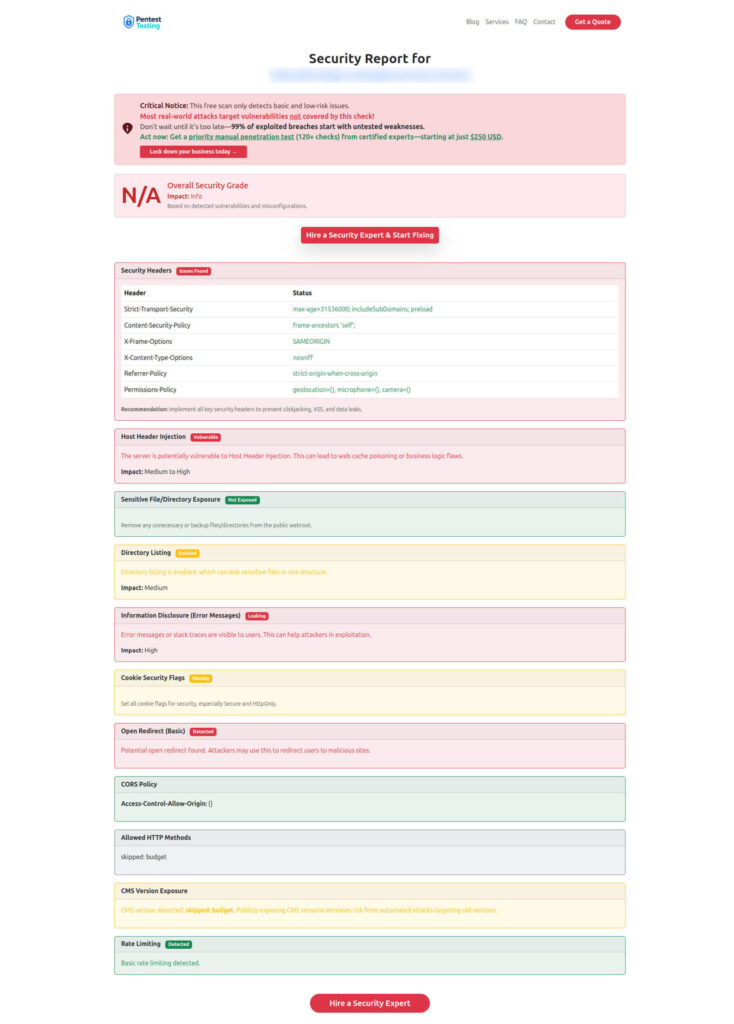
Sample scanner report to check Website Vulnerability
Related recent reads from our blog (recommended internal links)
- https://www.pentesttesting.com/post-patch-forensics-playbook-2026/
- https://www.pentesttesting.com/mobile-post-patch-validation-playbook/
- https://www.pentesttesting.com/rapid-dfir-checklist-patch-to-proof/
- https://www.pentesttesting.com/january-2026-patch-tuesday-smb-patch-first/
- https://www.pentesttesting.com/audit-ready-patch-evidence-pack/
- https://www.pentesttesting.com/windows-malware-forensics-memory-kape/
- https://www.pentesttesting.com/digital-forensics-am-i-hacked-dfir-triage/
- https://www.pentesttesting.com/iphone-suspicious-activity-dfir-checklist/
🔐 Frequently Asked Questions (FAQs)
Find answers to commonly asked questions about Forensic-Driven Security Hardening.