CVE-2026-20963 SharePoint: First 48-Hour Response
On March 18, 2026, CISA added CVE-2026-20963 to the Known Exploited Vulnerabilities catalog. NVD now lists it as a Microsoft Office SharePoint deserialization vulnerability that allows an unauthorized attacker to execute code over a network, and the KEV due date for federal agencies was set to March 21, 2026. Microsoft’s advisory was revised on March 17, including a corrected FAQ and a CVSS 3.1 vector of AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H with a 9.8 Critical base score.
For security teams running self-managed SharePoint, this is not a “patch when the change window opens” issue. It is a first-48-hours triage problem: confirm exposure, preserve evidence, contain safely, remediate fast, and validate that the environment is actually clean. Microsoft’s currently listed affected products are SharePoint Enterprise Server 2016, SharePoint Server 2019, and SharePoint Server Subscription Edition, with fixed versions published by Microsoft.
This guide is written for security buyers, IT leaders, and response teams who need a practical answer to one question: What should we do in the first 48 hours if we run vulnerable SharePoint?

What the KEV listing changes
A KEV entry changes the conversation. Once a vulnerability is listed there, the issue is no longer just a backlog item in vulnerability management. It becomes an urgent exposure and incident-readiness decision because CISA uses the KEV catalog for vulnerabilities with evidence of exploitation in the wild, and this one now carries a network-reachable, no-user-interaction, critical RCE profile. In practical terms, that means many teams should treat vulnerable SharePoint as a potential incident until they have enough evidence to rule compromise out.
It also changes who needs to be involved. This is not just a SharePoint admin patching task. It often requires coordination between infrastructure, security operations, DFIR, identity, backup, and application owners because patching without preserving evidence can erase the trail you need to determine whether exploitation already occurred.
Which environments should act immediately
Based on Microsoft’s advisory metadata, the vulnerable product families are:
- Microsoft SharePoint Enterprise Server 2016 before 16.0.5535.1001
- Microsoft SharePoint Server 2019 before 16.0.10417.20083
- Microsoft SharePoint Server Subscription Edition before 16.0.19127.20442
That means this article applies to self-managed SharePoint Server environments, not generic Microsoft 365 collaboration usage. If your organization only uses SharePoint Online and does not operate these server products, Microsoft’s affected product list for this CVE does not point to your environment in the same way.
Hours 0-4: Exposure triage before broad changes
The first four hours are about answering five questions quickly:
- Which SharePoint servers are in scope?
- Are any of them internet-facing or exposed through reverse proxy, VPN, partner access, or broad internal reachability?
- What exact build versions are running?
- Is there any early sign of suspicious execution, file changes, service changes, or unusual outbound traffic?
- Can you preserve enough evidence before you patch or isolate?
If you can answer those five questions well, your next 44 hours get much easier.
A simple starting point is a version and host inventory:
Add-PSSnapin Microsoft.SharePoint.PowerShell -ErrorAction SilentlyContinue
Get-SPFarm | Select-Object BuildVersion
Get-SPServer | Select-Object Address, Role, Status
(Get-Item "C:\Program Files\Common Files\microsoft shared\Web Server Extensions\16\ISAPI\Microsoft.SharePoint.dll").VersionInfo.FileVersionYou should also identify any internet-exposed VIPs, reverse proxies, load balancers, and WAF paths that publish SharePoint externally. For many organizations, the safest immediate move is not “patch first at all costs.” It is restrict exposure first where practical, then preserve, then patch. That is especially true if the environment is internet-facing and you do not yet know whether suspicious activity preceded your response.
Evidence to preserve before patching
This is the step many teams get wrong.
If you patch, reboot, recycle services, or rebuild before collecting evidence, you can destroy the timeline that tells you whether the vulnerability was merely present or actually used. Our own DFIR services emphasize the same principle: confirm what happened, preserve evidence, and then drive containment and recovery from evidence rather than guesswork.
At minimum, preserve:
- VM snapshots or storage snapshots, where approved
- IIS logs
- Windows Event Logs: Security, System, Application, PowerShell
- EDR telemetry and recent detections
- Recent file modifications in SharePoint web roots and extension paths
- Hashes of key binaries, configuration files, and modified artifacts
- Scheduled tasks, services, startup persistence, and new local admin assignments
- Outbound connection telemetry
- Any memory capture workflow your DFIR team is prepared to handle
A practical Windows evidence-preservation starter looks like this:
$case = "D:\IR\sharepoint-cve-2026-20963-$(Get-Date -Format yyyyMMdd-HHmmss)"
New-Item -ItemType Directory -Path $case -Force | Out-Null
robocopy "C:\inetpub\logs\LogFiles" "$case\IIS" /E /COPY:DAT
wevtutil epl Security "$case\Security.evtx"
wevtutil epl System "$case\System.evtx"
wevtutil epl Application "$case\Application.evtx"
wevtutil epl "Microsoft-Windows-PowerShell/Operational" "$case\PowerShell-Operational.evtx"
$targets = @(
"C:\inetpub\wwwroot\wss\VirtualDirectories",
"C:\Program Files\Common Files\microsoft shared\Web Server Extensions\16"
)
Get-ChildItem $targets -Recurse -File -ErrorAction SilentlyContinue |
Get-FileHash -Algorithm SHA256 |
Export-Csv "$case\sha256.csv" -NoTypeInformationYou should also create a short UTC case log that records who collected what, from which host, and when. That matters later if legal, audit, or customer-notification questions arise.
Containment decisions: isolate first, patch first, or both?
There is no single answer for every environment, but there is a clear decision pattern.
If the SharePoint environment is internet-facing and you have signs of suspicious activity, reduce exposure immediately. That may mean removing public publishing, restricting source IPs, disabling the external VIP, or forcing access through a narrower administrative path while evidence is preserved. After that, patch and validate.
If the environment is exposed but you do not yet have signs of compromise, do a fast evidence capture, patch all affected nodes, and validate versions and logs immediately after the change.
If you already have indicators of execution or persistence, this is no longer “urgent patching only.” It is incident response with remediation, and the goal is not just to close the vulnerability but to determine whether the attacker already established a foothold.
What you should avoid is the worst middle ground: patching one node, leaving others behind, skipping evidence, and assuming the issue is closed because the build number changed.
Hours 4-24: Hunt for execution, persistence, and follow-on abuse
Once minimum evidence is safe, the next phase is targeted hunting.
Look for:
- suspicious child processes launched by worker processes such as
w3wp.exe - PowerShell,
cmd.exe, or scripting activity tied to SharePoint hosts - unexpected changes to
web.config, application pools, IIS modules, or virtual directories - recent file writes in SharePoint-relevant directories
- new scheduled tasks or services
- unusual outbound traffic from SharePoint servers
- suspicious authentications or admin activity that may indicate lateral movement or credential abuse
Example hunting logic in a Windows-centric telemetry platform:
SecurityEvent
| where TimeGenerated > ago(7d)
| where EventID == 4688
| where NewProcessName endswith @"\powershell.exe"
or NewProcessName endswith @"\cmd.exe"
or NewProcessName endswith @"\cscript.exe"
or NewProcessName endswith @"\wscript.exe"
| project TimeGenerated, Computer, ParentProcessName, NewProcessName, CommandLine, AccountAnd a file-change hunt focused on likely web content and server-extension paths:
DeviceFileEvents
| where Timestamp > ago(7d)
| where FolderPath has @"\inetpub\wwwroot\wss\VirtualDirectories"
or FolderPath has @"\microsoft shared\Web Server Extensions\16"
| project Timestamp, DeviceName, ActionType, FolderPath, FileName, SHA256, InitiatingProcessFileNameEven if you do not find obvious webshell-style activity, that does not prove the host is clean. It only tells you whether your current data sources show something obvious. That is why log retention, EDR depth, and forensic readiness matter so much in the first 24 hours.
Hours 24-48: Remediate, harden, and verify
By the second day, the goal shifts from “respond fast” to “close cleanly.”
That means:
- patching every affected SharePoint node
- confirming the running build version matches Microsoft’s fixed releases
- reviewing whether any suspicious changes remain after patching
- checking service accounts, scheduled tasks, local admin memberships, and high-risk outbound connectivity
- documenting what was preserved, what was changed, and what was verified
This is also the right point to address the environment issues that often make SharePoint incidents worse than they needed to be:
- excessive internet exposure
- weak segmentation between SharePoint and the rest of the estate
- poor logging depth
- overly privileged service accounts
- inconsistent EDR coverage
- no repeatable incident evidence workflow
- no targeted retest after emergency remediation
That is where structured Remediation Services and a broader Risk Assessment Services engagement become useful, especially for regulated organizations that need a documented closure path rather than an informal “we patched it” statement. Our remediation service is built around documented compliance and technical fixes, while its risk assessment service focuses on gap analysis, prioritization, and action plans leadership teams can use.
When to escalate to DFIR
You should escalate from normal vulnerability response to DFIR when you see any of the following:
- suspicious process execution on the SharePoint host
- unexplained file modifications in web or server-extension paths
- signs of persistence, privilege escalation, or credential theft
- suspicious outbound traffic from SharePoint
- admin account anomalies or follow-on movement into adjacent systems
- regulated or sensitive data potentially exposed
- conflicting evidence that you cannot resolve with normal infrastructure troubleshooting
Our Digital Forensic Analysis Services explicitly arrange DFIR as evidence-backed investigation, preservation, and containment guidance across compromised devices, accounts, email, and cloud-linked incidents. That alignment matters here because the right outcome is not just “patched,” but “we know what happened, what was at risk, and what to do next.”
When to run validation testing after patching
Emergency patching closes the known hole. It does not validate the rest of the attack surface around it.
After patching, run targeted validation against:
- external publishing paths
- authentication and administrative exposure
- IIS hardening and logging configuration
- legacy components and custom SharePoint integrations
- exposed backups, old content paths, test pages, and weak configs
- adjacent web application risk that could still give attackers leverage
Our web application penetration testing service is designed as manual, exploit-focused testing with sample reporting and fix verification support. That is useful after emergency SharePoint remediation because stakeholders often need proof that the environment is not just patched, but also validated.
Our Website Vulnerability Scanner tool Dashboard
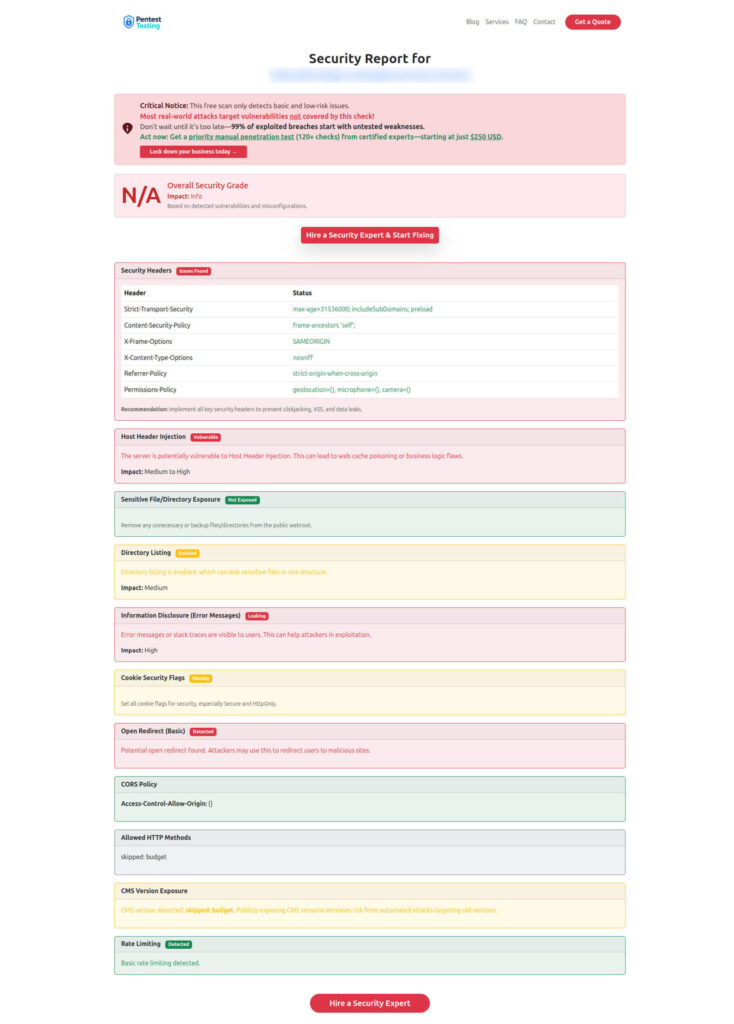
For a quick external checkpoint, our Free Website Vulnerability Scanner helps teams spot missing security headers, exposed files, weak cookie settings, information leakage, and other common web issues in minutes. It is useful for fast visibility and stakeholder reporting, but it should be treated as a quick exposure snapshot, not a replacement for SharePoint-specific incident triage, evidence preservation, or post-patch validation.
Sample report by our tool to check Website Vulnerability
Where Pentest Testing Corp fits in this response
If your organization is dealing with CVE-2026-20963 SharePoint right now, the most practical split is:
- use Digital Forensic Analysis Services when evidence preservation and incident reconstruction matter
- use Remediation Services when you need a documented technical closure path
- use Risk Assessment Services if the issue exposed broader governance, segmentation, or control gaps
- use the sample report to show internal stakeholders what professional fix validation and reporting should look like
That positioning matches how the site currently presents the business: manual-first testing, secure evidence handling, remediation guidance, optional retest support, and clear reporting for both engineering teams and leadership.
Related reading on Pentest Testing Corp
- Microsoft OAuth Redirect Abuse: First 48 Hours of Incident Triage for Microsoft 365 and Google Workspace
- Android March 2026 Bulletin: Evidence Preservation and Triage After Suspected Device Compromise
- Google Workspace Account Takeovers Without Passwords: Investigating OAuth App Abuse and Token Persistence
Final takeaway
The real risk with CVE-2026-20963 SharePoint is not only that it is patchable. It is that teams may patch too late, patch incompletely, or patch in a way that destroys the evidence needed to determine whether the server was already used as an entry point. In the first 48 hours, the winning sequence is simple: confirm exposure, preserve evidence, contain deliberately, remediate comprehensively, and validate the result. That is the difference between closing a ticket and closing an incident.
Request urgent scoping for SharePoint investigation and remediation if you need fast support for exposure review, evidence preservation, containment planning, remediation, or post-patch validation.
🔐 Frequently Asked Questions (FAQs)
Find answers to commonly asked questions about Microsoft SharePoint CVE-2026-20963.