Server-Side Request Forgery (SSRF Vulnerability) in WordPress
Server-Side Request Forgery (SSRF Vulnerability) in WordPress is a high-impact flaw where a WordPress site is tricked into making outbound requests to attacker-controlled URLs. Because those requests originate from the server, they may reach internal services (e.g., localhost, cloud metadata 169.254.169.254, container networks, or VPC-only assets) that are not publicly exposed. In the worst cases, SSRF in WordPress can lead to credential theft, data exfiltration, or pivoting deeper into your infrastructure.

This guide explains how SSRF happens in WordPress, shows secure coding patterns, and gives 7 proven fixes you can apply today.
✅ Quick win: If you suspect SSRF right now, immediately block egress to internal addresses (e.g.,
127.0.0.0/8,169.254.169.254,10.0.0.0/8,172.16.0.0/12,192.168.0.0/16, IPv6::1,fc00::/7) at the OS firewall level and review any plugin code that fetches URLs from user input.
Why SSRF Hits WordPress So Often
- Plugins and themes commonly fetch remote resources (webhooks, oEmbeds, image proxies, license ping, API calls) using functions like
wp_remote_get()or cURL. - If a developer accepts a user-supplied URL without robust validation, an attacker can point the site at internal targets.
- Redirect chains and DNS rebinding make naive “blocklist” checks unreliable.
- Shared hosting or weak egress controls exacerbate risk.
We’ll show you how to prevent Server-Side Request Forgery (SSRF Vulnerability) in WordPress with safe patterns that stand up to real-world tricks.
A Classic Anti-Pattern (Don’t Do This)
// BAD: vulnerable pattern.
add_action('wp_ajax_fetch_preview', function () {
if ( ! current_user_can('edit_posts') ) {
wp_send_json_error('Unauthorized', 403);
}
$url = isset($_POST['url']) ? $_POST['url'] : '';
// ❌ Directly using user input in wp_remote_get
$response = wp_remote_get($url);
if (is_wp_error($response)) {
wp_send_json_error($response->get_error_message(), 400);
}
wp_send_json_success(wp_remote_retrieve_body($response));
});Even with capability checks, this can be abused by any authenticated user role with access—or by CSRF if nonce/capability checks are missing. An attacker can submit http://127.0.0.1:8080/admin or http://169.254.169.254/latest/meta-data/ to pivot internally.
Safer, Allowlist-First Pattern
/**
* Validate a URL against strict rules to reduce SSRF risk.
* - Require http/https scheme
* - Enforce host allowlist
* - Resolve DNS and ensure all IPs are public (no private, loopback, link-local)
*/
function pt_is_public_ip(string $ip): bool {
// Normalize IPv4/IPv6 and check ranges
if (filter_var($ip, FILTER_VALIDATE_IP, FILTER_FLAG_IPV4)) {
$private = [
['10.0.0.0', '10.255.255.255'],
['172.16.0.0', '172.31.255.255'],
['192.168.0.0', '192.168.255.255'],
['127.0.0.0', '127.255.255.255'],
['169.254.0.0', '169.254.255.255'], // link-local incl. metadata 169.254.169.254
['0.0.0.0', '0.255.255.255'],
['100.64.0.0', '100.127.255.255'], // CGNAT
];
$ip_long = ip2long($ip);
foreach ($private as [$start, $end]) {
if ($ip_long >= ip2long($start) && $ip_long <= ip2long($end)) {
return false;
}
}
return true;
}
if (filter_var($ip, FILTER_VALIDATE_IP, FILTER_FLAG_IPV6)) {
// Block loopback, link-local, unique-local
$blocked = ['::1', 'fe80::', 'fc00::', 'fd00::'];
foreach ($blocked as $prefix) {
if (stripos($ip, $prefix) === 0) return false;
}
return true;
}
return false;
}
function pt_dns_resolves_to_public(string $host): bool {
$records = dns_get_record($host, DNS_A + DNS_AAAA);
if (empty($records)) return false;
foreach ($records as $rec) {
$ip = $rec['type'] === 'AAAA' ? $rec['ipv6'] : ($rec['ip'] ?? null);
if ($ip && ! pt_is_public_ip($ip)) return false;
}
return true;
}
function pt_is_url_allowed(string $url, array $allowlist_hosts): bool {
$parts = wp_parse_url($url);
if (empty($parts['scheme']) || ! in_array($parts['scheme'], ['http','https'], true)) return false;
if (empty($parts['host'])) return false;
$host = strtolower($parts['host']);
// Enforce an explicit allowlist (e.g., your API domains, whitelisted CDNs)
$allowed = array_map('strtolower', $allowlist_hosts);
$is_allowed_host = false;
foreach ($allowed as $allowed_host) {
if ($host === $allowed_host || str_ends_with('.' . $host, '.' . $allowed_host)) {
$is_allowed_host = true; break;
}
if ($host === $allowed_host || str_ends_with($host, '.' . $allowed_host)) {
$is_allowed_host = true; break;
}
}
if ( ! $is_allowed_host ) return false;
// Ensure resolution only to public IPs (mitigates SSRF + DNS rebinding)
return pt_dns_resolves_to_public($host);
}
add_action('wp_ajax_fetch_preview', function () {
check_ajax_referer('pt_preview_nonce');
if ( ! current_user_can('edit_posts') ) {
wp_send_json_error('Unauthorized', 403);
}
$url = isset($_POST['url']) ? esc_url_raw($_POST['url']) : '';
$allowlist = ['api.example.com','cdn.example.com'];
if ( ! pt_is_url_allowed($url, $allowlist) ) {
wp_send_json_error('Blocked by SSRF policy', 400);
}
// Prefer the "safe" wrapper and reject unsafe URLs in WP HTTP API:
$response = wp_safe_remote_get($url, [
'timeout' => 5,
'redirection' => 0, // no 30x hops to internal nets
'reject_unsafe_urls' => true, // WordPress arg to reject bad hosts/schemes
'user-agent' => 'PentestTesting/1.0',
]);
if (is_wp_error($response)) {
wp_send_json_error($response->get_error_message(), 400);
}
wp_send_json_success(wp_remote_retrieve_body($response));
});Why this helps: You’re using an allowlist, validating scheme/host, enforcing public IP resolution, limiting redirects, and invoking wp_safe_remote_get() with reject_unsafe_urls. That’s a robust starting point to prevent Server-Side Request Forgery (SSRF Vulnerability) in WordPress.
Screenshot of Pentest Testing Corp’s Website Vulnerability Scanner
Site-Wide Safety Net via Filters (Defense in Depth)
Even with good local validation, install a global interceptor so any plugin that calls the WordPress HTTP API still benefits:
/**
* Short-circuit outbound HTTP if the destination is unsafe (global net).
* Blocks private/loopback/link-local/metadata networks and non-allowlisted hosts.
*/
add_filter('pre_http_request', function ($preempt, $args, $url) {
$allowlist = ['api.example.com','cdn.example.com','*.trusted-vendor.com'];
if ( ! pt_is_url_allowed($url, $allowlist) ) {
return new WP_Error('ssrf_blocked', 'Outbound request blocked by SSRF policy.');
}
return false; // continue normally
}, 10, 3);This protects you if another plugin author forgot to sanitize a URL. It’s a pragmatic mitigation for SSRF in WordPress environments with many third-party components.
7 Proven Fixes for SSRF Vulnerability in WordPress
- Adopt an Allowlist for Outbound HTTP
Define the only domains your site may contact. Treat everything else as denied. - Enforce Public-Only Resolution
Validate that resolved A/AAAA records are not in private, loopback, link-local, or unique-local ranges. This is critical to stop Server-Side Request Forgery (SSRF Vulnerability) in WordPress from hitting metadata or internal services. - Disable Redirects for Untrusted Calls
Setredirectionto0unless you explicitly expect a known redirect chain within your allowlist. - Harden WordPress HTTP Calls
Preferwp_safe_remote_get()/wp_safe_remote_post()with'reject_unsafe_urls' => true. Set conservative timeouts and saneuser-agentstrings for observability. - Add a Global HTTP Interceptor
Usepre_http_request(above) to block anything not validated—especially helpful when plugins get updates you didn’t review.
- Implement Egress Firewall Rules
At the OS or platform level, block outbound connections to private ranges and metadata endpoints:
# Example (Linux): Block cloud metadata and loopback as egress
sudo iptables -A OUTPUT -d 169.254.169.254 -j REJECT
sudo iptables -A OUTPUT -d 127.0.0.0/8 -j REJECT
sudo iptables -A OUTPUT -d 10.0.0.0/8 -j REJECT
sudo iptables -A OUTPUT -d 172.16.0.0/12 -j REJECT
sudo iptables -A OUTPUT -d 192.168.0.0/16 -j REJECTOn cloud, prefer security groups / VPC egress ACLs to restrict destinations centrally.
- Add Auditing & Alerts
Log all outbound destinations and alert on new domains:
add_filter('http_api_debug', function($response, $type, $class, $args, $url) {
error_log('[HTTP DEBUG]['.$type.'] '.$url.' -> '. (is_wp_error($response) ? $response->get_error_message() : 'OK'));
}, 10, 5);This visibility helps you detect attempts to revive SSRF Vulnerability in WordPress via new attack chains.
Bonus: Secure Image Proxy (Common SSRF Hotspot)
If you proxy user-supplied images (for resizing/caching), you must lock it down:
function pt_secure_image_fetch( string $url ): string {
// Only allow http/https, public IPs, and specific media hosts (e.g., imgur, your CDN)
$allow = ['images.example.com','i.imgur.com','your-cdn.net'];
if ( ! pt_is_url_allowed($url, $allow) ) {
return '';
}
$res = wp_safe_remote_get($url, [
'timeout' => 5,
'redirection' => 0,
'reject_unsafe_urls' => true,
'headers' => ['Accept' => 'image/*'],
]);
if (is_wp_error($res)) return '';
$mime = wp_remote_retrieve_header($res, 'content-type');
if (strpos($mime, 'image/') !== 0) return '';
$body = wp_remote_retrieve_body($res);
// Store to uploads and return a local URL…
$filename = wp_unique_filename(wp_get_upload_dir()['path'], 'proxy-'.wp_hash($url).'.bin');
$path = trailingslashit(wp_get_upload_dir()['path']) . $filename;
file_put_contents($path, $body);
return trailingslashit(wp_get_upload_dir()['url']).$filename;
}WordPress-Friendly Helpers You Can Reuse
// Ensures scheme is http/https and passes WP's own URL validator
function pt_wp_validate_url(string $url): bool {
if ( ! in_array(wp_parse_url($url, PHP_URL_SCHEME), ['http','https'], true) ) return false;
return (bool) wp_http_validate_url($url); // WP helper (available in core)
}// Quick wrapper for GET with consistent safe defaults
function pt_safe_get(string $url, array $args = []) {
$defaults = [
'timeout' => 5,
'redirection' => 0,
'reject_unsafe_urls' => true,
'headers' => ['User-Agent' => 'PentestTesting/1.0'],
];
return wp_safe_remote_get($url, array_replace($defaults, $args));
}Testing & Verification Workflow
- Static review: Search your code for outbound calls:
wp_remote_get,wp_remote_post,wp_safe_remote_*,curl_exec,file_get_contents('http - Threat model: Identify endpoints where users provide URLs (webhooks, imports, oEmbeds, social previews).
- Try blocked targets: Confirm you cannot fetch
http://127.0.0.1/,http://[::1]/, orhttp://169.254.169.254/. - Redirect tests: Ensure redirects to private nets are blocked (set
redirection => 0). - Logging: Confirm HTTP debug logs record destinations to help catch SSRF Vulnerability in WordPress attempts early.
See Our Free Tool in Action
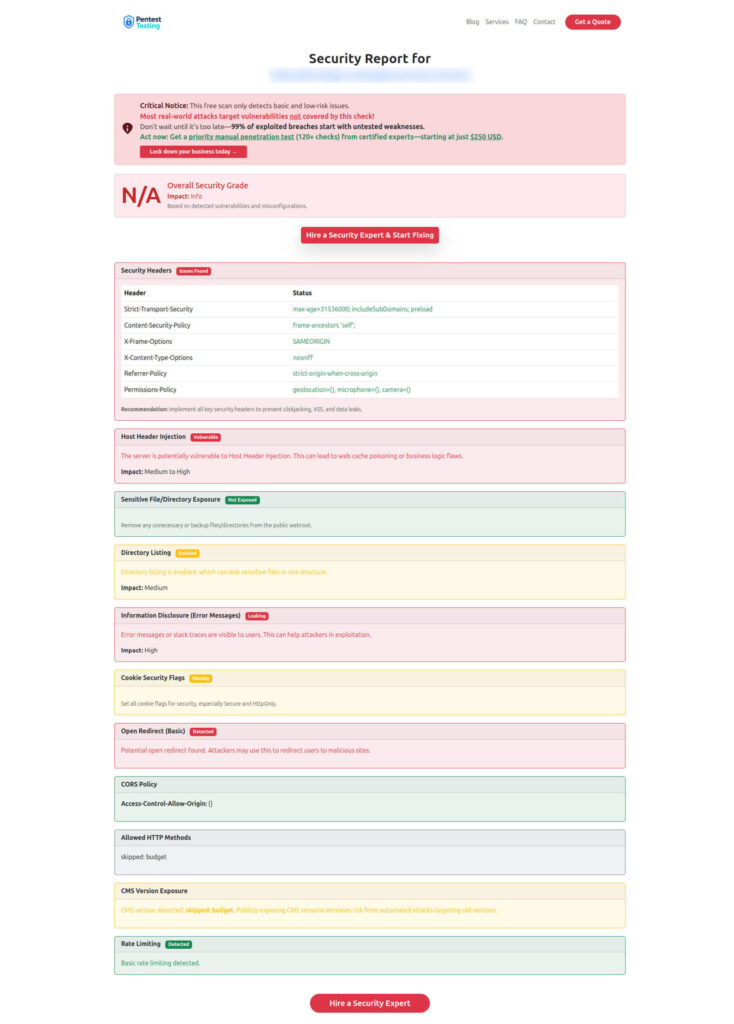
Sample Assessment Report by our free tool to check Website Vulnerability
Related Reading (From Our Network)
- Framework-specific hardening: Prevent XSSI Attack in Laravel
- WordPress Security hardening: XXE Injection in WordPress
- Frontend security edge case: Fix CRLF Injection in React.js
- Executive-friendly primer: Top 7 Cybersecurity Threats
- Case Study: ISO 27001 Remediation for a Wealth Firm
These resources complement your work on minimizing Server-Side Request Forgery (SSRF Vulnerability) in WordPress with broader secure-by-design practices.
Service Tracks That Help You Eliminate Risk
Managed IT Services (For Continuous Hardening)
Our Managed IT Services team can enforce egress filtering, centralize logging, and maintain WAF/IDS baselines so SSRF attempts are contained—without slowing down your release cadence.
AI Application Cybersecurity (For API-Heavy Apps)
Building AI-driven features or connecting to SaaS APIs? Our AI Application Cybersecurity service threat-models third-party calls, validates transformers that fetch external content, and tests SSRF defenses around retrieval pipelines.
Offer Cybersecurity to Your Clients (For Agencies/MSPs)
If you’re an agency or MSP, package our expertise under your brand with Offer Cybersecurity Service to Your Client. We’ll help you bake SSRF protections into client builds—scalable and profitable.
Developer Checklist (Copy/Paste)
- Replace all
wp_remote_get()on user input with an allowlist-validated helper. - Add
pre_http_requestfilter to enforce global SSRF policy. - Set
redirection => 0unless redirects are strictly needed within the allowlist. - Block egress to private/metadata IP ranges at OS or cloud perimeter.
- Log outbound domains and alert on new destinations.
- Review plugins after updates for any new outbound network features.
Try It Free: Scan Your Site Now
Before you push the next release, run a quick scan with our free tool for a Website Security check. You’ll get a prioritized report with SSRF-adjacent risks like open redirects, weak URL validation, and misconfigured firewalls—so your team can fix issues fast.
If you’d like us to review a specific plugin or custom integration for SSRF Vulnerability in WordPress, reach out through our service pages above. We’re happy to help your team ship safely, quickly, and confidently.
🔐 Frequently Asked Questions (FAQs)
Find answers to commonly asked questions about SSRF Vulnerability in WordPress.

