9 Powerful Risk-Based Authentication Controls Beyond MFA
Static MFA is no longer the finish line. It’s the baseline.
Modern attackers routinely work around “check-the-box” MFA through tactics like push fatigue, phishing-based session replay, token theft, and abuse of weak recovery flows. The fix isn’t “more MFA prompts.” It’s risk based authentication: continuously evaluating context and behavior, then applying the right control at the right moment.
This guide shows a practical, engineering-focused approach to authentication hardening using adaptive MFA, behavioral authentication, and identity risk scoring—with deployable patterns and code you can plug into real systems.

Need an expert assessment of your current auth posture and risk signals? Explore our Risk Assessment Services and Remediation Services.
1) Threat Landscape: How Static MFA Gets Bypassed
Static MFA usually asks one question: “Did the user provide a second factor?”
Risk-based authentication asks: “Does this login look legitimate right now—and should it be allowed, stepped up, or blocked?”
Common bypass themes (high level, defensive):
- Push fatigue / prompt bombing: users are spammed until one approval slips through.
- Phishing with replay: attackers capture credentials + MFA response and reuse sessions.
- Token/session theft: malware or exposed tokens bypass MFA entirely after login.
- Account recovery abuse: reset flows become the real “back door.”
- Device swap / SIM risk: weak recovery channels become the easiest path.
If your controls are identical for every login attempt, attackers can optimize against them.
2) Risk Signals That Actually Matter (Not Just IP)
A strong identity risk scoring model blends multiple signals so no single weak indicator decides the outcome.
High-signal categories
A) Device posture & binding
- Managed device compliance (MDM posture)
- Known device binding (per-account, per-app)
- Hardware-backed keys (passkeys / FIDO2)
B) Network & origin
- IP reputation (known bad / hosting / anonymizers)
- ASN / datacenter vs residential
- Impossible travel (coarse, not invasive)
C) Behavior & session anomaly (behavioral authentication)
- Login velocity, failed attempts, unusual timing
- New device + new country + sensitive action combo
- Unusual navigation right after login (e.g., export/keys/billing)
D) Transaction risk
- Sensitive operations (API key creation, payout change, role changes)
- High-impact admin actions
- New integrations/webhooks
Key principle: Don’t treat authentication as a single moment. Treat it as a risk-evaluated session lifecycle.
3) Build a Simple Risk Engine You Can Ship This Week
Risk-based authentication doesn’t need “AI magic.” Start with:
- Score (0–100)
- Reason codes
- Policy outcome: allow / step-up / deny
Example: Policy tiers (config-driven)
# auth-risk-policy.yaml
thresholds:
allow_max: 29
stepup_max: 69
deny_min: 70
weights:
new_device: 20
new_geo: 15
ip_reputation_bad: 30
impossible_travel: 25
failed_login_burst: 20
risky_action: 25
device_noncompliant: 40
token_anomaly: 35
stepup_methods:
preferred: ["passkey", "webauthn", "totp"]
fallback: ["backup_codes"]
last_resort: ["sms"] # keep as last resort where possibleExample: Risk scoring (Node.js/TypeScript)
type Signals = {
newDevice: boolean;
newGeo: boolean;
ipReputationBad: boolean;
impossibleTravel: boolean;
failedLoginBurst: boolean;
riskyAction: boolean;
deviceNoncompliant: boolean;
tokenAnomaly: boolean;
};
type Decision = {
score: number;
outcome: "allow" | "step_up" | "deny";
reasons: string[];
};
export function computeRisk(signals: Signals): Decision {
const reasons: string[] = [];
let score = 0;
const add = (cond: boolean, points: number, reason: string) => {
if (!cond) return;
score += points;
reasons.push(reason);
};
add(signals.newDevice, 20, "new_device");
add(signals.newGeo, 15, "new_geo");
add(signals.ipReputationBad, 30, "ip_reputation_bad");
add(signals.impossibleTravel, 25, "impossible_travel");
add(signals.failedLoginBurst, 20, "failed_login_burst");
add(signals.riskyAction, 25, "risky_action");
add(signals.deviceNoncompliant, 40, "device_noncompliant");
add(signals.tokenAnomaly, 35, "token_anomaly");
let outcome: Decision["outcome"] = "allow";
if (score >= 70) outcome = "deny";
else if (score >= 30) outcome = "step_up";
return { score, outcome, reasons };
}Example: Express middleware that enforces risk gates
import type { Request, Response, NextFunction } from "express";
import crypto from "crypto";
import { computeRisk } from "./risk";
function requestId() {
return crypto.randomBytes(8).toString("hex");
}
export async function riskGate(req: Request, res: Response, next: NextFunction) {
const rid = requestId();
res.setHeader("x-request-id", rid);
// Example signals (replace with your actual collectors)
const signals = {
newDevice: req.headers["x-known-device"] !== "true",
newGeo: req.headers["x-geo-new"] === "true",
ipReputationBad: req.headers["x-ip-bad"] === "true",
impossibleTravel: req.headers["x-impossible-travel"] === "true",
failedLoginBurst: req.headers["x-fail-burst"] === "true",
riskyAction: req.path.includes("/admin") || req.path.includes("/api-keys"),
deviceNoncompliant: req.headers["x-device-compliant"] === "false",
tokenAnomaly: req.headers["x-token-anomaly"] === "true",
};
const decision = computeRisk(signals);
// Attach decision for logging + downstream authorization
(req as any).authRisk = { ...decision, requestId: rid };
if (decision.outcome === "deny") {
return res.status(403).json({ error: "blocked_by_risk_policy", request_id: rid });
}
if (decision.outcome === "step_up") {
// Redirect to step-up (or return 401 with a structured challenge)
return res.status(401).json({
error: "step_up_required",
request_id: rid,
risk_score: decision.score,
reasons: decision.reasons,
next: "STEP_UP_FLOW",
});
}
return next();
}4) Adaptive Authentication Models That Work in Production
A) Step-up authentication (context scoring → higher assurance)
Don’t step-up every login. Step-up when the context is risky.
Common step-up triggers:
- New device + sensitive action
- Admin role change
- Export/download spikes
- Recovery flow usage
- New geo + token anomaly
B) Risk gates (allow / step-up / block)
Risk based authentication should produce deterministic outcomes:
- Allow: silent, low friction
- Step-up: passkey/TOTP/hardware key
- Deny: block + require support or verified recovery
C) Transaction verification for high-impact actions
For certain actions (payout changes, new API keys), use:
- step-up and
- explicit confirmation, plus audit logging
5) Practical Step-Up With OIDC (Identity Provider Friendly)
If you use an Identity Provider (IdP), you can implement step-up by requesting a higher assurance context during authentication.
Example: Request step-up using OIDC parameters (server side)
// Pseudocode: build an authorization request that asks for higher assurance
const authUrl = new URL(process.env.OIDC_AUTHORIZATION_ENDPOINT!);
authUrl.searchParams.set("client_id", process.env.OIDC_CLIENT_ID!);
authUrl.searchParams.set("response_type", "code");
authUrl.searchParams.set("redirect_uri", process.env.OIDC_REDIRECT_URI!);
authUrl.searchParams.set("scope", "openid profile email");
// Ask for recent auth + higher assurance context
authUrl.searchParams.set("max_age", "300"); // re-auth if older than 5 min
authUrl.searchParams.set("acr_values", "urn:loa:2"); // your IdP’s “step-up” level
// Carry your risk context for correlation (don’t put secrets here)
authUrl.searchParams.set("state", `risk:${requestId}`);
return res.redirect(authUrl.toString());Example: Verify assurance in the returned ID token claims
// Pseudocode: after token exchange, validate "acr" and "amr" claims
const acr = idTokenClaims.acr; // e.g., "urn:loa:2"
const amr = idTokenClaims.amr || []; // e.g., ["pwd","webauthn"]
if (expectedStepUp && acr !== "urn:loa:2") {
throw new Error("Step-up not satisfied");
}
if (expectedPasskey && !amr.includes("webauthn")) {
throw new Error("Passkey not satisfied");
}6) Phishing-Resistant MFA: Add Passkeys (WebAuthn) for High-Risk Paths
For step-up, prioritize phishing-resistant options:
- Passkeys (WebAuthn/FIDO2)
- Hardware security keys
- TOTP (better than SMS, but still phishable)
Minimal WebAuthn step-up (high level)
Browser (step-up prompt):
// Pseudocode: step-up using WebAuthn in the browser
const options = await fetch("/webauthn/authenticate/options").then(r => r.json());
const credential = await navigator.credentials.get({ publicKey: options });
await fetch("/webauthn/authenticate/verify", {
method: "POST",
headers: { "content-type": "application/json" },
body: JSON.stringify(credential),
});Server (verify response and elevate session):
// Pseudocode: verify WebAuthn assertion, then mark session as "elevated"
app.post("/webauthn/authenticate/verify", async (req, res) => {
// verifyAssertion(req.body) -> true/false (library-dependent)
const ok = await verifyAssertion(req.body);
if (!ok) return res.status(401).json({ error: "step_up_failed" });
req.session.assurance = "elevated";
req.session.elevated_until = Date.now() + 10 * 60 * 1000; // 10 minutes
return res.json({ status: "ok" });
});7) Device Posture: Verify “Compliant Device” Claims (Don’t Trust Headers)
If you rely on device compliance, validate it cryptographically.
Example: Verify a signed posture token (JWT)
import jwt from "jsonwebtoken";
type Posture = { device_id: string; compliant: boolean; ts: number; };
export function verifyDevicePosture(postureJwt: string, publicKeyPem: string): Posture {
const payload = jwt.verify(postureJwt, publicKeyPem, {
algorithms: ["RS256"],
clockTolerance: 10,
}) as any;
// Basic freshness check (e.g., 5 min)
if (Date.now() - payload.ts * 1000 > 5 * 60 * 1000) {
throw new Error("stale_device_posture");
}
return payload as Posture;
}Use the result as a risk input, not a single-point decision.
8) Fallback Channels Without Creating a Recovery Back Door
Attackers love recovery flows. Keep them:
- rate-limited
- risk-gated
- auditable
- resistant to social engineering
A safe pattern: “recovery requires step-up too”
- If user can’t step-up, require verified recovery and delay
- Notify user out-of-band
- Log everything with correlation IDs
9) Logging & Telemetry for Authentication Risk Signals
If you want risk based authentication to hold up under incident response, logging must capture:
- what signals were used
- what decision was made
- why (reason codes)
- what step-up method succeeded
- correlation identifiers across app + IdP
Minimum viable auth-risk event (JSON)
{
"ts": "2026-03-03T09:15:12.012Z",
"request_id": "req_7f91a2c3",
"trace_id": "4b3b0c1c2f2b1a9e",
"user_id": "u_123",
"tenant_id": "t_9",
"session_id": "s_456",
"event": "auth_decision",
"route": "POST /login",
"risk_score": 62,
"outcome": "step_up",
"reasons": ["new_device", "ip_reputation_bad", "risky_action"],
"auth": {
"mfa_method": "webauthn",
"assurance": "elevated"
}
}OpenTelemetry attributes (app-layer visibility)
import { context, trace } from "@opentelemetry/api";
export function annotateRisk(decision: any) {
const span = trace.getSpan(context.active());
if (!span) return;
span.setAttribute("auth.risk.score", decision.score);
span.setAttribute("auth.risk.outcome", decision.outcome);
span.setAttribute("auth.risk.reasons", decision.reasons.join(","));
}Forensic Implications: What to Capture and Retain
If authentication abuse occurs, responders need to answer:
- Which sessions were created, elevated, and from where?
- Which signals triggered step-up or block?
- Was recovery invoked?
- Which IdP events align with the app session?
Practical data model (SQL)
CREATE TABLE auth_risk_events (
id BIGSERIAL PRIMARY KEY,
ts TIMESTAMPTZ NOT NULL,
request_id TEXT NOT NULL,
trace_id TEXT NULL,
user_id TEXT NULL,
tenant_id TEXT NULL,
session_id TEXT NULL,
event TEXT NOT NULL, -- auth_decision, stepup_success, recovery_attempt, etc.
route TEXT NULL,
risk_score INT NOT NULL,
outcome TEXT NOT NULL, -- allow, step_up, deny
reasons JSONB NOT NULL, -- ["new_device", "ip_reputation_bad"]
ip TEXT NULL,
user_agent TEXT NULL,
device_id TEXT NULL,
idp_event_id TEXT NULL
);
CREATE INDEX idx_auth_risk_events_user_ts ON auth_risk_events (user_id, ts DESC);
CREATE INDEX idx_auth_risk_events_session_ts ON auth_risk_events (session_id, ts DESC);Retention guidance (practical):
- Keep auth decisions + step-up outcomes long enough for investigations and compliance needs.
- Store reason codes (not raw sensitive data), and hash identifiers where appropriate.
If you suspect a compromise, our Digital Forensic Analysis Services can help reconstruct timelines and confirm scope.
Integration Tips: IdPs, IAM, and Access Management
Risk-based authentication works best when your app, gateway, and IdP share a consistent story:
- Use OIDC/SAML consistently (don’t mix ad-hoc auth shortcuts)
- Centralize policy and make it auditable
- Use SCIM or your IAM workflows for lifecycle control
- Correlate IdP sign-in events with app request IDs / trace IDs
Where to Start (Fast Wins Checklist)
- Implement risk scoring + reason codes (even if simple).
- Add step-up for risky sessions and sensitive actions.
- Prioritize passkeys/WebAuthn for step-up.
- Harden recovery: rate-limit + risk-gate + alert.
- Emit structured auth-risk logs + trace correlation.
- Review gaps via Risk Assessment Services and fix with Remediation Services.
Free Website Vulnerability Scanner Tool Page (Dashboard)
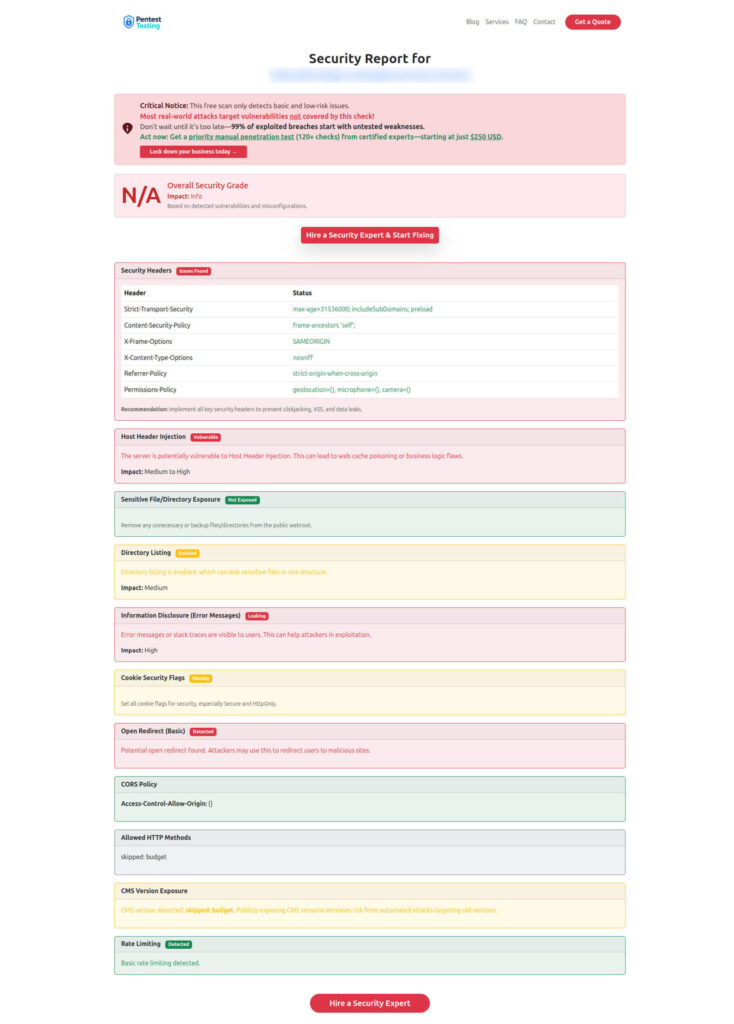
Sample Report from our tool to check Website Vulnerability
Related Recent Reads From Our Blog
- 7 Powerful Steps to API Logic Abuse Detection
- 9 Proven API Abuse Detection Plays WAFs Miss
- 7 Powerful Risk-Driven API Throttling Tactics
- 7 Powerful Server-Side Template Injection Defenses
- 7 Powerful Forensic Readiness Steps for SMBs
- 9 Powerful Forensic-Driven Security Hardening Steps
🔐 Frequently Asked Questions (FAQs)
Find answers to commonly asked questions about Risk Based Authentication & Adaptive MFA.