Adaptive Webhook Security: Real-Time Validation, Filtering & Incident Evidence
Webhooks are “push” automation: a public endpoint that triggers internal workflows. That’s exactly why attackers target them. A single forged or replayed event can cause real business impact—refunds, privilege changes, CI/CD deployments, account takeovers, or silent data exposure.
This guide shows webhook security best practices you can implement as a layered, real-time control plane—so inbound events are validated, filtered, rate-controlled, and logged with forensic-ready evidence. You’ll get practical code patterns for Node.js, Python, Nginx, and test harnesses that safely exercise edge cases.

If you want an expert-led review of your exposure and prioritized fixes, start with our Risk Assessment Services:
https://www.pentesttesting.com/risk-assessment-services/
1) Incoming webhook threats you must model first
Treat every webhook as untrusted input even when it’s from a “trusted vendor.” Common attack paths we see in webhook penetration testing:
SSRF via “convenient” webhook fields
SSRF often happens indirectly: the webhook payload contains a url, callback, avatar, document_link, or similar—then your code fetches it server-side.
Bad pattern (SSRF-prone):
// ❌ Never fetch untrusted URLs from webhook payloads
const { url } = req.body;
const resp = await fetch(url);Safer pattern (allowlist + egress control):
// ✅ Allowlist domains + deny private ranges (still use egress firewall)
import { URL } from "node:url";
import dns from "node:dns/promises";
import ipaddr from "ipaddr.js";
const ALLOWED_HOSTS = new Set(["cdn.vendor.com", "files.vendor.com"]);
async function assertSafeUrl(raw) {
const u = new URL(raw);
if (u.protocol !== "https:") throw new Error("Only https URLs allowed");
if (!ALLOWED_HOSTS.has(u.hostname)) throw new Error("Host not allowed");
// Resolve and block private IP space (defense-in-depth)
const { address } = await dns.lookup(u.hostname);
const ip = ipaddr.parse(address);
const range = ip.range();
if (["private", "loopback", "linkLocal", "uniqueLocal"].includes(range)) {
throw new Error("Resolved to private IP space");
}
}Replay attacks (valid event, resent later)
Attackers don’t need to break crypto if you accept old events. Any signed webhook can be replayed unless you enforce freshness + idempotency.
Malformed payloads and parser abuse
Oversized bodies, deep JSON objects, decompression bombs, XML entity tricks, multipart boundary abuse can cause downtime, queue floods, or security bypasses.
Spoofed events and weak verification
Common mistakes:
- verifying the HMAC of parsed JSON instead of raw bytes
- missing a timestamp check
- using non-constant time string comparison
- trusting IP allowlists without cryptographic proof
2) Adaptive validation layers (the real-time “stack”)
Strong webhook threat mitigation is layered. A solid baseline looks like:
- Transport controls: TLS only, strict cipher defaults (at your edge)
- Authentication proof: HMAC signature or mTLS where supported
- Freshness: timestamp window
- Idempotency: store event IDs with TTL (reject duplicates)
- Schema enforcement: strict payload shape + limits
- Filtering: allowlist event types + field-level policies
- Rate limits: global + per-vendor + per-IP + per-event-type
- Anomaly detection: sudden spikes, unusual event types, signature fails
- Forensic logging: capture evidence without storing secrets unsafely
3) Signed webhooks + trust validation (HMAC done correctly)
Node.js (Express) — capture raw body for HMAC
import express from "express";
import crypto from "crypto";
const app = express();
// ✅ Capture raw body bytes (must happen before parsing)
app.use(express.json({
limit: "256kb",
verify: (req, res, buf) => { req.rawBody = buf; },
}));
function timingSafeHexEqual(a, b) {
const ba = Buffer.from(a, "hex");
const bb = Buffer.from(b, "hex");
if (ba.length !== bb.length) return false;
return crypto.timingSafeEqual(ba, bb);
}
function assertFreshTimestamp(tsHeader, maxSkewSeconds = 300) {
const ts = Number(tsHeader);
if (!Number.isFinite(ts)) throw new Error("Invalid timestamp");
const now = Math.floor(Date.now() / 1000);
if (Math.abs(now - ts) > maxSkewSeconds) throw new Error("Stale webhook");
}
function verifyHmac({ rawBody, timestamp, signature, secret }) {
const msg = Buffer.concat([Buffer.from(`${timestamp}.`), rawBody]);
const digest = crypto.createHmac("sha256", secret).update(msg).digest("hex");
const sig = signature.startsWith("sha256=") ? signature.slice(7) : signature;
return timingSafeHexEqual(digest, sig);
}Idempotency (Redis) — stop replays before side effects
import { createClient } from "redis";
const redis = createClient({ url: process.env.REDIS_URL });
await redis.connect();
async function assertIdempotent(eventId, ttlSeconds = 86400) {
if (!eventId) throw new Error("Missing event id");
const key = `webhook:seen:${eventId}`;
const ok = await redis.set(key, "1", { NX: true, EX: ttlSeconds });
if (ok !== "OK") throw new Error("Duplicate webhook (replay)");
}Secure receiver route (end-to-end)
const ALLOWED_TYPES = new Set(["invoice.paid", "build.completed", "user.updated"]);
app.post("/webhooks/vendor", async (req, res) => {
try {
const signature = req.header("x-webhook-signature") || "";
const timestamp = req.header("x-webhook-timestamp") || "";
const eventId = req.header("x-webhook-id") || "";
assertFreshTimestamp(timestamp, 300);
await assertIdempotent(eventId, 86400);
const secret = process.env.WEBHOOK_SIGNING_SECRET;
if (!secret) throw new Error("Server misconfigured");
if (!verifyHmac({ rawBody: req.rawBody, timestamp, signature, secret })) {
return res.status(401).json({ error: "Invalid signature" });
}
// ✅ Only now treat it as “trusted enough” to parse & route
const event = req.body;
if (!ALLOWED_TYPES.has(event.type)) {
return res.status(400).json({ error: "Unsupported event type" });
}
// ✅ Push to queue; avoid doing heavy work inline
// await queue.publish(event);
return res.status(200).json({ received: true });
} catch (e) {
return res.status(400).json({ error: e.message });
}
});Python (FastAPI) — constant-time compare + freshness
import hmac, hashlib, time
from fastapi import FastAPI, Header, Request, HTTPException
app = FastAPI()
def verify(ts: str, sig: str, raw: bytes, secret: str) -> bool:
msg = f"{ts}.".encode() + raw
digest = hmac.new(secret.encode(), msg, hashlib.sha256).hexdigest()
if sig.startswith("sha256="):
sig = sig[7:]
return hmac.compare_digest(digest, sig)
@app.post("/webhooks/vendor")
async def webhook(
request: Request,
x_webhook_signature: str = Header(default=""),
x_webhook_timestamp: str = Header(default=""),
):
raw = await request.body()
try:
ts = int(x_webhook_timestamp)
except Exception:
raise HTTPException(400, "Invalid timestamp")
now = int(time.time())
if abs(now - ts) > 300:
raise HTTPException(400, "Stale webhook")
secret = "LOAD_FROM_SECRET_MANAGER"
if not verify(x_webhook_timestamp, x_webhook_signature, raw, secret):
raise HTTPException(401, "Invalid signature")
payload = await request.json()
return {"received": True, "type": payload.get("type")}HMAC key rotation (practical pattern)
Support multiple active secrets: current + previous (for vendor delivery delays).
function verifyWithRotation(args, secrets) {
for (const s of secrets) {
if (verifyHmac({ ...args, secret: s })) return true;
}
return false;
}mTLS (when your provider supports it)
If the webhook sender can present a client certificate, enforce mutual TLS at your edge. Example (conceptual Nginx):
server {
listen 443 ssl;
ssl_certificate /etc/ssl/certs/server.crt;
ssl_certificate_key /etc/ssl/private/server.key;
ssl_client_certificate /etc/ssl/certs/vendor_ca.crt;
ssl_verify_client on;
location /webhooks/vendor {
proxy_pass http://app;
}
}4) Schema enforcement: strict webhook validation without breaking vendors
Even “valid” signed events can contain dangerous or unexpected data. Strong webhook validation prevents injection, parsing abuse, and logic bypass.
JSON Schema enforcement (Node.js + AJV)
import Ajv from "ajv";
const ajv = new Ajv({ allErrors: true, removeAdditional: "failing" });
const schema = {
type: "object",
additionalProperties: false,
required: ["id", "type", "created_at", "data"],
properties: {
id: { type: "string", minLength: 8, maxLength: 128 },
type: { type: "string", maxLength: 64 },
created_at: { type: "integer" },
data: {
type: "object",
additionalProperties: true
}
}
};
const validate = ajv.compile(schema);
function assertSchema(payload) {
const ok = validate(payload);
if (!ok) throw new Error("Schema validation failed");
}Limit size + depth (prevent parser DoS)
- enforce
Content-Lengthlimits at edge (e.g., 256 KB) - reject deeply nested objects (common DoS vector)
function assertMaxDepth(obj, maxDepth = 12, depth = 0) {
if (depth > maxDepth) throw new Error("Payload too deep");
if (obj && typeof obj === "object") {
for (const v of Object.values(obj)) assertMaxDepth(v, maxDepth, depth + 1);
}
}5) Filtering strategies for JSON, XML, and multipart bodies
A) JSON filtering: allowlist fields you actually use
A clean pattern: transform into an internal canonical event and discard everything else.
function normalizeEvent(incoming) {
return {
id: incoming.id,
type: incoming.type,
occurredAt: incoming.created_at,
// Only keep what the workflow needs
actorId: incoming?.data?.actor?.id ?? null,
objectId: incoming?.data?.object?.id ?? null,
};
}B) XML: disable entity expansion + forbid DTDs
If you must accept XML webhooks, do it with hardened parsers and strict limits.
Python (defused XML parsing):
from defusedxml.ElementTree import fromstring
def parse_safe_xml(raw: bytes):
# defusedxml blocks many entity-based attacks
root = fromstring(raw)
return root.tagPolicy tip: Prefer converting to JSON at a controlled boundary and validate the resulting structure.
C) Multipart: lock down fields, file sizes, and types
Use strict limits and only accept expected parts.
import Busboy from "busboy";
function parseMultipart(req) {
return new Promise((resolve, reject) => {
const bb = Busboy({
headers: req.headers,
limits: { fileSize: 2 * 1024 * 1024, files: 1, fields: 10 }
});
const out = { fields: {}, file: null };
bb.on("field", (name, val) => {
if (!["event_id", "type"].includes(name)) return; // ignore unexpected fields
out.fields[name] = val;
});
bb.on("file", (name, file, info) => {
const { mimeType } = info;
if (name !== "attachment") return file.resume();
if (!["application/pdf", "image/png"].includes(mimeType)) {
file.resume();
return reject(new Error("Unsupported file type"));
}
const chunks = [];
file.on("data", (d) => chunks.push(d));
file.on("end", () => { out.file = Buffer.concat(chunks); });
});
bb.on("finish", () => resolve(out));
bb.on("error", reject);
req.pipe(bb);
});
}6) Adaptive controls: real-time validation that changes with risk
“Adaptive” means you don’t treat every event equally. Example signals:
- vendor identity / integration tier
- event type sensitivity (refund vs. read-only update)
- recent signature failures or replay attempts
- source IP anomalies (if vendor publishes stable IP ranges)
- request rate spikes
Simple policy-as-code (YAML)
vendors:
vendorA:
maxBody: 262144
maxSkewSec: 300
requireIdempotency: true
allowedTypes: ["invoice.paid", "invoice.refunded"]
rateLimitPerMin: 120
vendorB:
maxBody: 131072
maxSkewSec: 120
requireIdempotency: true
allowedTypes: ["build.completed"]
rateLimitPerMin: 60Runtime policy enforcement (Node.js)
function getPolicy(vendor) {
const policies = {
vendorA: { maxSkewSec: 300, allowedTypes: new Set(["invoice.paid","invoice.refunded"]) },
vendorB: { maxSkewSec: 120, allowedTypes: new Set(["build.completed"]) },
};
return policies[vendor] || null;
}
function assertPolicy(policy, event) {
if (!policy.allowedTypes.has(event.type)) throw new Error("Type not allowed by policy");
}7) Incident evidence: webhook incident logging for forensic readiness
Most teams log “something happened.” During an incident, you need proof:
- raw request hash (integrity)
- timestamp, headers (sanitized), IP, request ID, signature status
- event ID, vendor, event type, decision outcome
- correlation IDs across queue/worker/storage
Evidence-friendly structured logging (Node.js)
import crypto from "crypto";
function sha256(buf) {
return crypto.createHash("sha256").update(buf).digest("hex");
}
function auditLog({ req, outcome, reason }) {
const rawHash = req.rawBody ? sha256(req.rawBody) : null;
console.log(JSON.stringify({
at: new Date().toISOString(),
route: req.path,
method: req.method,
ip: req.headers["cf-connecting-ip"] || req.ip,
userAgent: req.headers["user-agent"],
contentType: req.headers["content-type"],
contentLength: req.headers["content-length"],
webhookId: req.headers["x-webhook-id"],
ts: req.headers["x-webhook-timestamp"],
sigPresent: Boolean(req.headers["x-webhook-signature"]),
rawSha256: rawHash, // ✅ tamper-evident reference
outcome, // "accepted" | "rejected"
reason // short reason code (no secrets)
}));
}For deeper investigations and evidence handling, our DFIR team can help you design log retention and chain-of-custody workflows:
https://www.pentesttesting.com/digital-forensic-analysis-services/
8) Automated test harnesses: safely exercise edge cases
Automated webhook validation tests catch regressions after every release.
Pytest: signature + replay + schema tests (conceptual)
import time, hmac, hashlib, json
import requests
SECRET = b"test_secret"
def sign(ts, raw):
msg = f"{ts}.".encode() + raw
return hmac.new(SECRET, msg, hashlib.sha256).hexdigest()
def test_valid_event():
ts = str(int(time.time()))
payload = {"id":"evt_12345678","type":"invoice.paid","created_at":int(ts),"data":{"object":{"id":"inv_1"}}}
raw = json.dumps(payload).encode()
headers = {
"x-webhook-timestamp": ts,
"x-webhook-signature": "sha256=" + sign(ts, raw),
"x-webhook-id": "evt_12345678",
"content-type": "application/json",
}
r = requests.post("https://YOURDOMAIN/webhooks/vendor", data=raw, headers=headers, timeout=5)
assert r.status_code == 200
def test_replay_rejected():
ts = str(int(time.time()))
payload = {"id":"evt_replay","type":"invoice.paid","created_at":int(ts),"data":{}}
raw = json.dumps(payload).encode()
headers = {
"x-webhook-timestamp": ts,
"x-webhook-signature": "sha256=" + sign(ts, raw),
"x-webhook-id": "evt_replay",
"content-type": "application/json",
}
r1 = requests.post("https://YOURDOMAIN/webhooks/vendor", data=raw, headers=headers, timeout=5)
r2 = requests.post("https://YOURDOMAIN/webhooks/vendor", data=raw, headers=headers, timeout=5)
assert r1.status_code == 200
assert r2.status_code in (400, 409)k6 load test: rate-limits + queue safety
import http from "k6/http";
import { check, sleep } from "k6";
export const options = { vus: 20, duration: "30s" };
export default function () {
const url = "https://YOURDOMAIN/webhooks/vendor";
const payload = JSON.stringify({ id: "evt_"+__ITER__, type: "build.completed", created_at: Date.now()/1000|0, data: {} });
const params = { headers: { "Content-Type": "application/json" } };
const r = http.post(url, payload, params);
check(r, { "status is ok-ish": (res) => [200, 202, 400, 401, 429].includes(res.status) });
sleep(0.1);
}9) Remediation playbooks + proof-of-fix verification
When webhook issues are found, fix them in a repeatable order:
- Block obvious abuse fast: edge rate-limit + body size caps + TLS only
- Add cryptographic proof: HMAC verification using raw bytes (or mTLS)
- Add replay protection: timestamp window + idempotency store
- Harden parsing: schema enforcement + safe XML/multipart handling
- Add filtering: allowlist event types + canonicalize fields
- Add telemetry: structured audit logs + anomaly alerts
- Prove the fix: run automated harness + targeted negative tests
- Lock in changes: CI checks for “signature required” and “idempotency required” routes
If you want us to implement or validate fixes end-to-end (including proof-of-fix testing), use our Remediation Services:
https://www.pentesttesting.com/remediation-services/
Free Website Vulnerability Scanner tool page (dashboard)
Sample assessment report to check Website Vulnerability
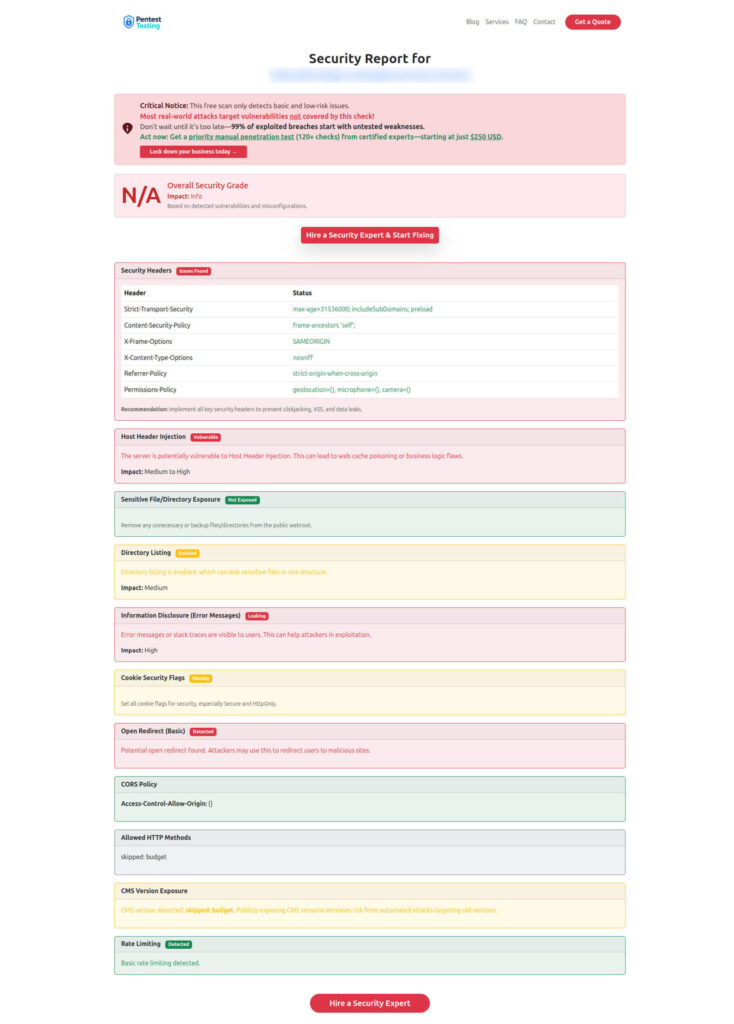
When you want a fast baseline check
Start with the blog hub (more hardening guides and checklists):
https://www.pentesttesting.com/blog/
And if you want quick signal on your external surface, use the free scanner:
https://free.pentesttesting.com/
Related reading on our blog (internal)
- Webhook security patterns and receiver examples: https://www.pentesttesting.com/webhook-security-best-practices/
- API logic abuse detection guardrails: https://www.pentesttesting.com/api-logic-abuse-detection-risk-scoring/
- Risk-based authentication hardening: https://www.pentesttesting.com/risk-based-authentication-hardening/
- API abuse detection beyond WAFs: https://www.pentesttesting.com/api-abuse-detection-waf-evasion/
- Forensic readiness log retention: https://www.pentesttesting.com/forensic-readiness-smb-log-retention/
🔐 Frequently Asked Questions (FAQs)
Find answers to commonly asked questions about Webhook Security Best Practices.