RCE Exploits in WordPress: A Practical, Developer-First Guide
RCE Exploits in WordPress (remote code execution) let an attacker run arbitrary code on your server—often leading to full site takeover, data theft, or malware drops. In the WordPress ecosystem, where plugins and themes expand functionality, one insecure handler, upload endpoint, or deserialization call can open the door. This guide shows you how RCE Exploits typically happen, how to detect them early, and how to write safer code patterns. You’ll also find actionable hardening steps, incident-response tips, and references to services and tools that make prevention easier.

Why RCE Exploits Are So Dangerous for WordPress
- Privilege escalation: Once code executes, attackers can create admin users, plant webshells, or pivot into your infrastructure.
- Stealth: Many payloads hide behind benign endpoints (e.g., AJAX actions, REST routes).
- Plugin/theme sprawl: The combinatorial surface area multiplies misconfigurations and stale code.
TL;DR: Treat RCE Exploits in WordPress as severity: critical and align your dev process to prevent the root causes.
Common Paths to RCE in WordPress (With Safer Patterns)
Below are frequent anti-patterns that lead to RCE Exploits in WordPress, plus secure alternatives you can drop into your codebase. Examples are illustrative; adapt to your plugin/theme architecture.
1) Insecure AJAX Handlers (missing nonces & caps)
Anti-pattern (don’t ship this):
// BAD: Missing nonce + capability checks; unsafely using eval().
add_action('wp_ajax_nopriv_run_code', 'ptc_run_code');
add_action('wp_ajax_run_code', 'ptc_run_code');
function ptc_run_code() {
$code = $_POST['code'] ?? '';
// ⚠️ evaluates attacker-supplied code
eval($code);
wp_send_json_success('OK');
}Safer pattern:
// GOOD: Nonce + capability + no eval + strict allowlist behavior
add_action('wp_ajax_run_task', 'ptc_run_task');
function ptc_run_task() {
check_ajax_referer('ptc_task_nonce', 'nonce');
if ( ! current_user_can('manage_options') ) {
wp_send_json_error('Unauthorized', 403);
}
$task = isset($_POST['task']) ? sanitize_text_field($_POST['task']) : '';
$allowed = ['flush_cache', 'reindex'];
if ( ! in_array($task, $allowed, true) ) {
wp_send_json_error('Invalid task', 400);
}
// Execute only pre-defined server-side functions
if ($task === 'flush_cache') {
ptc_flush_cache();
} elseif ($task === 'reindex') {
ptc_reindex();
}
wp_send_json_success('Done');
}2) Dangerous Deserialization (PHP Object Injection)
Anti-pattern:
// BAD: Untrusted unserialize()
$payload = base64_decode($_POST['data'] ?? '');
$object = unserialize($payload); // ⚠️ object injection → RCE gadgets
process_data($object);Safer pattern:
// GOOD: Use JSON; if you must unserialize, disallow classes.
$payload = wp_unslash($_POST['data'] ?? '');
$data = json_decode($payload, true, 512, JSON_THROW_ON_ERROR);
// Or: $data = unserialize($payload, ['allowed_classes' => false]);
process_data($data);3) Arbitrary File Uploads to Executable Paths
Anti-pattern:
// BAD: Accepts any file; stores in executable directory.
if (!empty($_FILES['file']['tmp_name'])) {
move_uploaded_file($_FILES['file']['tmp_name'], ABSPATH . 'wp-content/uploads/' . $_FILES['file']['name']);
echo 'uploaded';
}Safer pattern (PHP + web server rules):
$allowed_mimes = ['image/jpeg','image/png','application/pdf'];
$file = $_FILES['file'] ?? null;
if ($file && in_array($file['type'], $allowed_mimes, true)) {
require_once ABSPATH . 'wp-admin/includes/file.php';
$overrides = ['test_form' => false, 'mimes' => $allowed_mimes];
$result = wp_handle_upload($file, $overrides);
if (isset($result['error'])) {
wp_die('Upload failed.');
}
echo esc_url_raw($result['url']);
} else {
wp_die('Invalid file type.');
}Block PHP in uploads (Apache):
# .htaccess inside wp-content/uploads/
<Files *.php>
deny from all
</Files>Block PHP in uploads (Nginx):
location ~* /wp-content/uploads/.*\.php$ { return 403; }4) Remote File Inclusion / Insecure Includes
Anti-pattern:
// BAD: Directly including user-controlled path
include $_GET['view'] . '.php';Safer pattern:
$allowed_views = ['dashboard','reports','settings'];
$view = isset($_GET['view']) ? sanitize_key($_GET['view']) : 'dashboard';
if (!in_array($view, $allowed_views, true)) {
$view = 'dashboard';
}
include __DIR__ . '/views/' . $view . '.php';5) Command Execution via system()/shell_exec()
Anti-pattern:
// BAD: Pipes user input into shell
$ip = $_GET['ip'] ?? '127.0.0.1';
echo shell_exec("ping -c 1 " . $ip);Safer pattern:
$ip = filter_input(INPUT_GET, 'ip', FILTER_VALIDATE_IP, FILTER_FLAG_NO_PRIV_RANGE | FILTER_FLAG_NO_RES_RANGE);
if (!$ip) {
wp_die('Invalid IP');
}
echo esc_html(ptc_safe_ping($ip)); // implement with sockets or built-in PHP functions, no shell6) SQL Injection Gadgets → RCE Chaining
Use $wpdb->prepare() religiously; an SQL injection sometimes becomes a stepping-stone to RCE.
global $wpdb;
$user_id = (int) $_GET['id'];
$row = $wpdb->get_row( $wpdb->prepare("SELECT * FROM {$wpdb->users} WHERE ID = %d", $user_id) );7) REST Routes Without Permissions Callbacks
Anti-pattern:
register_rest_route('ptc/v1', '/run', [
'methods' => 'POST',
'callback' => 'ptc_run',
// ⚠️ no permission check
]);Safer pattern:
register_rest_route('ptc/v1', '/run', [
'methods' => 'POST',
'callback' => 'ptc_run',
'permission_callback' => function() {
return current_user_can('manage_options');
},
]);Scan Your Site Fast (Free) — Catch Issues Before RCE Hits
Run a quick health check and share the results with your team.
Screenshot of our Website Vulnerability Scanner tools homepage
While you’re scanning, you can also explore related security topics we’ve covered, like fixing broken access control in WordPress or preventing logic bugs similar to XSSI attacks in React that often coexist with high-impact flaws.
Developer Playbook: Detecting RCE Exploits in WordPress
Codebase Hunt: Grep for Red Flags
Use this during code reviews or CI checks to reduce RCE Exploits in WordPress risk:
# Dangerous PHP functions (investigate BEFORE you refactor)
grep -RniE "eval\(|assert\(|system\(|passthru\(|shell_exec\(|proc_open\(|popen\(|`[^`]*`" \
wp-content/plugins wp-content/themes
# Serialization landmines
grep -RniE "unserialize\(|serialize\(" wp-content/plugins wp-content/themesWP-CLI for Quick Hygiene
# List out-of-date plugins (patch windows matter for RCE)
wp plugin list --update=available --format=table
# Core + plugin updates
wp core update
wp plugin update --allMinimal MU-Plugin Hardening Snippet
Create wp-content/mu-plugins/ptc-hardening.php:
<?php
/**
* Plugin Name: PTC Hardening
*/
// Disable file editors
if (!defined('DISALLOW_FILE_EDIT')) {
define('DISALLOW_FILE_EDIT', true);
}
// Block execution in uploads via runtime checks (belt & suspenders)
add_action('init', function() {
$script_path = realpath($_SERVER['SCRIPT_FILENAME'] ?? '');
if ($script_path && str_contains($script_path, wp_normalize_path(WP_CONTENT_DIR . '/uploads/'))) {
status_header(403);
exit;
}
});
// Enforce JSON not PHP serialization across custom endpoints
add_filter('ptc_use_json_only', '__return_true');KSES & Output Escaping
$title = wp_kses( $_POST['title'] ?? '', ['a'=>['href'=>[]],'strong'=>[],'em'=>[]] );
echo esc_html( $title ); // or esc_url/esc_attr based on contextRead Your Report & Prioritize Fixes
After you scan, your report highlights misconfigurations and outdated components. Use it to triage:
Sample assessment report by our free tool to check Website Vulnerability
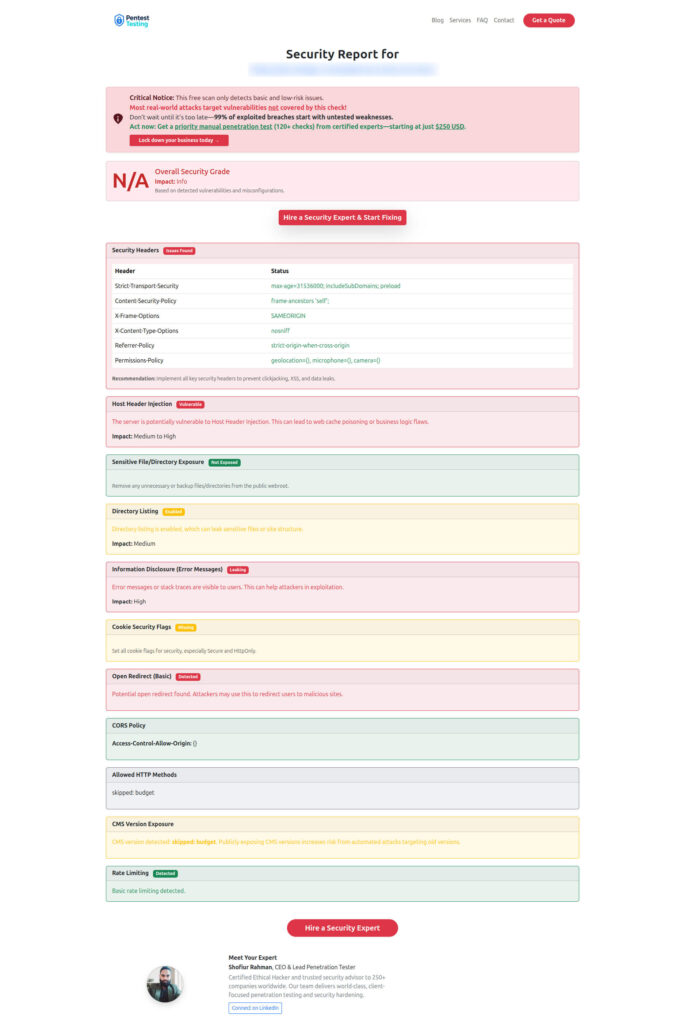
Quick triage order for RCE Exploits in WordPress:
- Publicly exploitable RCE (patch or disable vulnerable plugin/theme immediately).
- File upload misconfigs (block PHP in uploads, validate MIME, move to object storage).
- Deserialization & eval (refactor to JSON, remove dynamic code).
- REST/AJAX endpoints without checks (add nonce, capability checks, rate limits).
10 Proven Defenses Against RCE Exploits in WordPress
- Eliminate
eval()and shell calls; replace with safe server-side functions. - Always require nonces + capability checks (
check_ajax_referer,current_user_can). - Use JSON instead of
unserialize(); if unavoidable, setallowed_classes => false. - Block PHP in uploads via
.htaccessor Nginx config and never trust MIME alone. - Pin and update dependencies (composer libraries, vendor code) in CI.
- Use
$wpdb->prepare()for all dynamic queries. - Whitelist includes: never include user-provided paths.
- Harden file permissions (no
0644→ executable; limit write paths). - Add a WAF layer (hosted or server-level) to filter exploit patterns.
- Continuous scanning with our free website security scanner and scheduled patching.
These steps, consistently applied, dramatically shrink the window for RCE Exploits in WordPress.
Incident Response: If You Suspect RCE Right Now
- Isolate the site (maintenance mode, temporarily restrict public access).
- Capture forensic copies before cleaning: filesystem + DB + web server logs.
- Revoke secrets (salts/keys in
wp-config.php, API keys, tokens). - Remove webshells/backdoors (scan for
eval,base64_decode, and strange cron jobs). - Patch/disable the vulnerable component; restore known-good code from version control.
- Rotate credentials (DB, SFTP/SSH, admin accounts) and audit users.
- Add monitoring (integrity checks, file diffing, log alerts).
Related Reads & Cross-Framework Security
- WordPress: Fix Broken Access Control in WordPress
- Laravel: Prevent Sensitive Data Exposure in Laravel
- Frontend: Stop XSSI Attack in React.js
- AI/Apps: AI App Security Audit for ML/AI-driven products
- Case Study: ISO 27001 Remediation for an Australian Wealth Firm
These complement your strategy against RCE Exploits in WordPress by addressing adjacent risks and modern stacks.
Services to Help You Ship Securely
Managed IT for Secure Operations
Lock down endpoints, patching cadence, and network controls with our Managed IT Services. This creates the operational foundation that limits the blast radius of RCE Exploits in WordPress.
AI Application Cybersecurity
If you’re building AI features or LLM-powered plugins, our AI Application Cybersecurity service assesses model endpoints, prompt injection risks, and supply-chain dependencies—common pivot points attackers use after an RCE foothold.
For Agencies & MSPs
Offer world-class security to clients with our partner-friendly model: Offer Cybersecurity Service to Your Client. We help you deliver continuous assessments, remediation roadmaps, and training.
Copy-Paste Secure Defaults (Quick Reference)
Nonce fields in forms:
wp_nonce_field('ptc_task_nonce', 'nonce');Verify nonce in handlers:
check_ajax_referer('ptc_task_nonce', 'nonce');Strict input patterns (regex):
$slug = isset($_GET['slug']) ? sanitize_key($_GET['slug']) : '';
if (!preg_match('/^[a-z0-9\-]{3,40}$/', $slug)) { wp_die('Bad slug'); }Disallow file edits (wp-config.php):
define('DISALLOW_FILE_EDIT', true);Lock down uploads (re-stated because it’s vital):
# .htaccess in uploads
<FilesMatch "\.ph(p[0-9]?|ar|ps|tml)$">
Deny from all
</FilesMatch>Final Take
Preventing RCE Exploits in WordPress isn’t about one silver bullet—it’s about disciplined patterns: remove dynamic execution, validate and escape everything, guard every endpoint, and scan continuously. If you want an expert review or hands-on remediation, we’re ready to help—start with a quick pass for a Website Security check and we’ll meet you where you are.
🔐 Frequently Asked Questions (FAQs)
Find answers to commonly asked questions about RCE Exploits in WordPress.

