7 Powerful Steps to API Logic Abuse Detection
Beyond Static Scans: Continuous API Logic Abuse Detection with Runtime Guardrails
Traditional scanners and one-time API tests are great at finding known technical flaws. But real incidents increasingly come from logic abuse: valid requests, valid auth, and “normal-looking” traffic—used in harmful sequences to drain value, bypass workflow intent, or trigger costly downstream work.
This guide shows how to build continuous API security by adding runtime API guardrails, dynamic API risk scoring, and post-deploy gates that catch logic abuse and chained workflows in real time.
Just published: Risk-Based Authentication Hardening Beyond MFA — practical identity risk scoring, step-up policies, and forensic-ready logging.
https://www.pentesttesting.com/risk-based-authentication-hardening/If you want expert validation across authorization, abuse controls, and business-critical flows, explore our API Penetration Testing and Risk Assessment Services.
1) Why scanners miss API logic abuse (and why it matters)
Most scanners focus on:
- Single-request issues (headers, misconfigurations, injections, known CVEs)
- Stateless analysis (one endpoint at a time)
- “Is it vulnerable?” rather than “Is the workflow being abused?”
API logic abuse detection is different because the abuse often lives in:
- Sequences (Endpoint A → B → C)
- State (cart, coupon, OTP, payout, subscription tier)
- Cost asymmetry (one request triggers expensive DB/queue/report work)
- Low-and-slow behavior (stays under basic thresholds)
Bottom line: You need runtime visibility + stateful enforcement for continuous API security.
2) Anatomy of modern API logic abuse: sequences + state
Here are common logic-abuse shapes (described defensively, so teams can model guardrails):
A) Workflow bypass
Skipping steps:
- “Create draft order” → jump to “finalize” without payment state
- “Verify email/OTP” not required before sensitive operations
B) Replay + idempotency failures
- Replaying “apply credit” or “redeem coupon” calls
- Retrying payment/payout endpoints without idempotency keys
C) Race conditions (concurrency abuse)
- Parallel calls to “reserve inventory” or “claim offer”
- Winning an unintended state by timing (especially in distributed systems)
D) Cost-amplification abuse
- Hitting “export/report/search” endpoints that fan out into heavy work
Your guardrails should treat these as state transitions with invariants—not just “requests”.
3) Runtime guardrail concepts (breakpoints, sanity checks, adaptive throttles)
Think of runtime guardrails as policy + telemetry + enforcement at the exact points where value can be drained.
Guardrail Type 1: “Breakpoints” (enforce workflow state)
A breakpoint is a runtime check that says:
“This endpoint is only valid if the session/order/account is in state X.”
Example invariant: you cannot call POST /checkout/confirm unless payment_status == "authorized".
Guardrail Type 2: Sanity checks (detect “valid but wrong”)
Sanity checks validate business invariants:
- cart totals match line items
- coupon use counts and eligibility match rules
- payout amounts match account limits and KYC status
- export size matches plan/role entitlements
Guardrail Type 3: Adaptive throttles (risk-based, not flat limits)
Flat limits answer: “how many requests?”
Adaptive throttles answer: “how risky is this behavior right now?”
Signals to feed throttling:
- principal concurrency
- repeated errors (422/404/409 patterns)
- unusual endpoint sequences
- cost score (estimated DB/queue work per request)
4) Practical instrumentation: traces, session lifecycle, dynamic risk scoring
If you can’t measure it, you can’t detect it—especially for logic abuse.
A) Structured log event (minimum viable schema)
{
"ts": "2026-02-26T12:34:56.789Z",
"request_id": "req_9f2c",
"trace_id": "4f3a...c12",
"tenant_id": "t_123",
"principal_type": "user",
"principal_id": "u_991",
"session_id": "s_abcd",
"route": "POST /checkout/confirm",
"workflow": "checkout",
"state_before": "payment_authorized",
"state_after": "confirmed",
"http_status": 200,
"latency_ms": 143,
"cost_hint": 8,
"risk_score": 22
}B) OpenTelemetry trace enrichment (Node.js example)
import { context, trace } from "@opentelemetry/api";
export function enrichSpan(req, res, next) {
const span = trace.getSpan(context.active());
if (span) {
span.setAttribute("http.route", req.route?.path || req.path);
span.setAttribute("principal.id", req.user?.id || "anonymous");
span.setAttribute("tenant.id", req.user?.tenantId || "none");
span.setAttribute("session.id", req.headers["x-session-id"] || "none");
}
next();
}C) Session lifecycle tracking (Redis)
Track “last N endpoints” and concurrency per principal:
import Redis from "ioredis";
const redis = new Redis(process.env.REDIS_URL);
export async function trackSession(req, _res, next) {
const principal = req.user?.id || req.ip;
const keySeq = `seq:${principal}`;
const endpointClass = `${req.method} ${req.baseUrl}${req.path}`;
await redis.multi()
.lpush(keySeq, endpointClass)
.ltrim(keySeq, 0, 19) // keep last 20
.expire(keySeq, 3600)
.exec();
next();
}D) Dynamic API risk scoring (simple, practical starter)
function computeRisk({ route, status, latencyMs, costHint, seqAnomaly, concurrency }) {
let risk = 0;
// High-value endpoints are more sensitive
if (route.includes("/checkout") || route.includes("/payout") || route.includes("/export")) risk += 10;
// Repeated client errors can indicate probing/automation
if ([401, 403, 404, 409, 422].includes(status)) risk += 4;
// Latency spikes can indicate downstream stress
if (latencyMs > 800) risk += 6;
// Cost-aware: expensive endpoints should be guarded more aggressively
risk += Math.min(10, costHint || 0);
// Behavioral signals
if (seqAnomaly) risk += 8;
if (concurrency > 6) risk += 8;
return risk;
}5) Real-time runtime guardrails (code you can ship)
Below are production-friendly patterns for runtime API guardrails.
A) Breakpoint: enforce state machine for a workflow (checkout example)
const allowedTransitions = {
cart_open: new Set(["payment_authorized"]),
payment_authorized: new Set(["confirmed"]),
confirmed: new Set([]),
};
export function enforceStateTransition({ loadState, saveState }) {
return async (req, res, next) => {
const orderId = req.params.orderId;
const action = req.headers["x-workflow-action"]; // e.g., "confirmed"
const stateBefore = await loadState(orderId);
const allowed = allowedTransitions[stateBefore]?.has(action);
if (!allowed) {
return res.status(409).json({
error: "Invalid workflow transition",
orderId,
stateBefore,
attempted: action,
});
}
// Let handler run, then update state on success
res.locals._stateBefore = stateBefore;
res.locals._action = action;
return next();
};
}B) Sanity check: validate invariant (cart totals, coupon rules)
from decimal import Decimal
def assert_cart_invariants(cart):
# Example invariants (adapt to your model)
items_total = sum(Decimal(i["price"]) * i["qty"] for i in cart["items"])
if items_total != Decimal(cart["items_total"]):
raise ValueError("Cart invariant failed: items_total mismatch")
if cart.get("coupon"):
if cart["coupon"]["discount_amount"] > items_total:
raise ValueError("Cart invariant failed: discount exceeds total")C) Idempotency keys for “money/value” endpoints
import crypto from "crypto";
import Redis from "ioredis";
const redis = new Redis(process.env.REDIS_URL);
export function requireIdempotencyKey(ttlSeconds = 86400) {
return async (req, res, next) => {
const key = req.headers["idempotency-key"];
if (!key) return res.status(400).json({ error: "Missing Idempotency-Key" });
const bodyHash = crypto.createHash("sha256").update(JSON.stringify(req.body || {})).digest("hex");
const idemKey = `idem:${req.user.id}:${req.path}:${key}`;
const existing = await redis.get(idemKey);
if (existing && existing !== bodyHash) {
return res.status(409).json({ error: "Idempotency-Key reuse with different payload" });
}
const ok = await redis.set(idemKey, bodyHash, "EX", ttlSeconds, "NX");
if (!ok) {
return res.status(409).json({ error: "Duplicate request (idempotency hit)" });
}
next();
};
}D) Cost-based throttling (token bucket via Redis Lua)
Use “cost” (not just request count) to protect expensive endpoints.
-- token_bucket.lua
-- KEYS[1] = bucket key
-- ARGV[1] = now_ms
-- ARGV[2] = refill_rate_per_ms
-- ARGV[3] = capacity
-- ARGV[4] = cost
local key = KEYS[1]
local now = tonumber(ARGV[1])
local rate = tonumber(ARGV[2])
local cap = tonumber(ARGV[3])
local cost = tonumber(ARGV[4])
local data = redis.call("HMGET", key, "tokens", "ts")
local tokens = tonumber(data[1]) or cap
local ts = tonumber(data[2]) or now
local delta = math.max(0, now - ts)
tokens = math.min(cap, tokens + delta * rate)
if tokens < cost then
redis.call("HMSET", key, "tokens", tokens, "ts", now)
redis.call("PEXPIRE", key, 60000)
return 0
end
tokens = tokens - cost
redis.call("HMSET", key, "tokens", tokens, "ts", now)
redis.call("PEXPIRE", key, 60000)
return 1Node caller example:
import fs from "fs";
import Redis from "ioredis";
const redis = new Redis(process.env.REDIS_URL);
const lua = fs.readFileSync("./token_bucket.lua", "utf8");
const sha = await redis.script("LOAD", lua);
export async function costThrottle(req, res, next) {
const principal = req.user?.id || req.ip;
const key = `bucket:${principal}:${req.path}`;
const now = Date.now();
const cost = req.path.includes("/export") ? 10 : 2; // tune per endpoint
const allowed = await redis.evalsha(sha, 1, key, now, 0.002, 30, cost); // refill, cap
if (allowed === 0) return res.status(429).json({ error: "Too Many Requests (cost throttle)" });
next();
}E) FastAPI middleware variant (risk + guardrails)
from fastapi import FastAPI, Request
from starlette.responses import JSONResponse
import time
app = FastAPI()
@app.middleware("http")
async def runtime_guardrails(request: Request, call_next):
t0 = time.time()
response = await call_next(request)
latency_ms = int((time.time() - t0) * 1000)
path = request.url.path
status = response.status_code
# Example: tighten behavior on sensitive endpoints
if path.startswith("/payout") and status >= 400:
# Replace with your alert pipeline / SIEM forwarder
print("GUARDRAIL_SIGNAL", {"path": path, "status": status, "latency_ms": latency_ms})
return response6) Detection workflows: automated parsing + alerts for triage teams
You’ll get the best results when “detection” produces:
- a short incident record (who/what/when)
- the last N steps in the workflow
- supporting telemetry (trace IDs, request IDs, state transitions)
A) Minimal Python log parser (risk threshold + grouping)
import json
from collections import defaultdict
THRESHOLD = 25
def load_events(path):
with open(path, "r", encoding="utf-8") as f:
for line in f:
yield json.loads(line)
alerts = defaultdict(list)
for e in load_events("api_events.jsonl"):
if e.get("risk_score", 0) >= THRESHOLD:
key = (e.get("tenant_id"), e.get("principal_id"))
alerts[key].append(e)
for (tenant, principal), items in alerts.items():
items.sort(key=lambda x: x["ts"])
print("ALERT", tenant, principal, "events=", len(items))
print(" last_route=", items[-1].get("route"))
print(" last_trace=", items[-1].get("trace_id"))B) What to page on (high-signal)
- Invalid workflow transitions (409s) on sensitive flows
- Cost throttles firing repeatedly on export/report endpoints
- High concurrency for a single principal (API key / user / token)
- Suspicious sequence patterns (same 2–3 endpoints repeating)
7) Remediation playbooks: pattern fixes + proofs of fix + evidence capture
API abuse remediation is faster when you standardize on playbooks.
Playbook A: Workflow bypass / state abuse
Fix:
- enforce state machine at handler boundary
- store state transitions as immutable events (audit trail)
Prove fix: - add runtime test that attempts invalid transition and expects 409
Evidence: - attach trace + request IDs + state_before/state_after logs
Playbook B: Replay/idempotency failures
Fix:
- require idempotency keys on value endpoints
- dedupe on
(principal, endpoint, idem_key)
Prove fix: - send same request twice → second must be blocked or safely replayed
Evidence: - show idempotency hit logs + stable response behavior
Playbook C: Cost amplification (exports/search/report)
Fix:
- cost-based throttling + caching + async job queues
- restrict export size/fields by plan/role
Prove fix: - load test export endpoints under controlled conditions with cost enforcement enabled
Evidence: - demonstrate reduced DB timeouts/queue depth under simulated abuse
If you need a guided, prioritized fix plan after findings, use Remediation Services.
Connecting into continuous delivery: runtime tests as post-deploy gates
Static tests in CI are necessary—but logic abuse often appears after deployment (real traffic shapes + real integrations).
A) Post-deploy gate (GitHub Actions example)
name: post-deploy-api-guardrails
on:
workflow_run:
workflows: ["deploy"]
types: [completed]
jobs:
guardrail-tests:
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@v4
- name: Install k6
run: |
sudo apt-get update
sudo apt-get install -y gnupg
curl -s https://dl.k6.io/key.gpg | sudo gpg --dearmor -o /usr/share/keyrings/k6-archive-keyring.gpg
echo "deb [signed-by=/usr/share/keyrings/k6-archive-keyring.gpg] https://dl.k6.io/deb stable main" | sudo tee /etc/apt/sources.list.d/k6.list
sudo apt-get update && sudo apt-get install -y k6
- name: Run guardrail flow tests
env:
BASE_URL: ${{ secrets.BASE_URL }}
API_TOKEN: ${{ secrets.API_TOKEN }}
run: k6 run tests/guardrails.jsB) k6 runtime flow test (assert invariants)
import http from "k6/http";
import { check, sleep } from "k6";
const BASE = __ENV.BASE_URL;
const TOKEN = __ENV.API_TOKEN;
export default function () {
const headers = { Authorization: `Bearer ${TOKEN}`, "Content-Type": "application/json" };
// Example: attempt an invalid workflow transition and expect a block
const res = http.post(`${BASE}/checkout/confirm`, JSON.stringify({ orderId: "test-order" }), { headers });
check(res, {
"blocked invalid transition": (r) => [400, 401, 403, 409].includes(r.status),
});
sleep(1);
}This is how you operationalize continuous API security: deployments don’t pass if guardrails regress.
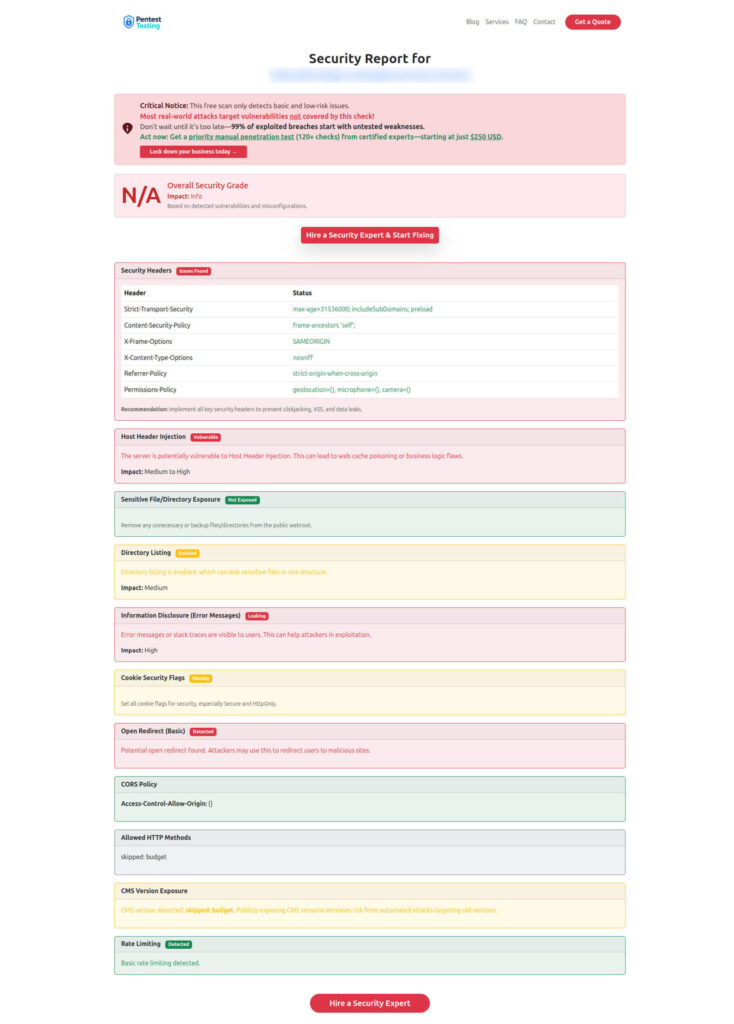
Free tool page + Sample report
Free Website Vulnerability Scanner Tool Page (Dashboard)
Sample Report to check Website Vulnerability
Practical next steps (do this this week)
- Pick 2 high-value workflows (checkout, payout, export) and model them as a state machine.
- Add structured logs + trace enrichment for tenant/principal/session/workflow state.
- Implement idempotency + cost throttles on value endpoints.
- Create 3 post-deploy guardrail tests that must block invalid transitions.
- Review results with a pentest-style “abuse lens” via API Penetration Testing.
If you suspect active abuse or need evidence-grade timelines, see Digital Forensic Analysis Services.
Related recent reads from our blog
- 9 Proven API Abuse Detection Plays WAFs Miss
- 7 Powerful Risk-Driven API Throttling Tactics
- 9 Powerful Webhook Security Patterns That Stop Breaches
- 7 Powerful Endpoint Deception Strategies to Contain Breaches
- 7 Powerful Forensic Readiness Steps for SMBs
🔐 Frequently Asked Questions (FAQs)
Find answers to commonly asked questions about API Logic Abuse Detection.
